Sponsored by PhishLabs
Sponsored by Forcepoint
Unlocking Business Success: The Five Pillars Of User Risk Mitigation
Sponsored by Forcepoint
Defeating The Threat Within
Sponsored by Forcepoint
Cyber Dwell Time and Lateral Movement
Sponsored by DataGravity
ESG Report: Continuous Sensitive Data Monitoring
Sponsored by Bit9+Carbon Black
Breach Preparation: Plan for the Inevitability of Compromise
Sponsored by IBM
Cyber Security Intelligence Index
Sponsored by Proofpoint
The Cybercrime Economics of Malicious Macros
Sponsored by BAE Systems
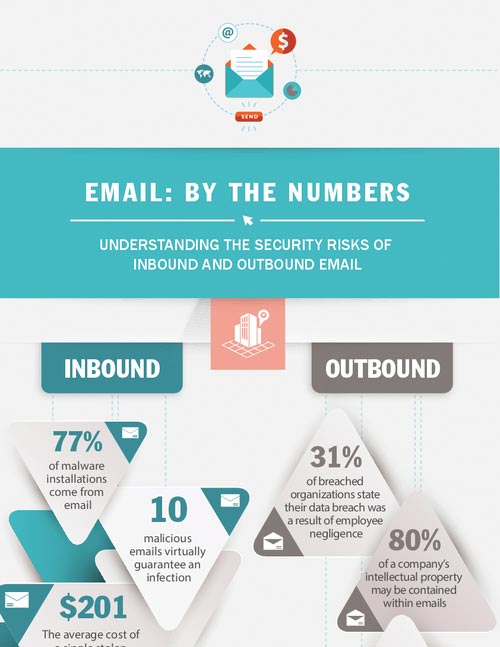
Email Risk: By The Numbers
Sponsored by BAE Systems
Five Strategies For Email Data Loss Prevention For Retailers
Sponsored by BAE Systems
Picking A Sensible Mobile Password Policy
Sponsored by BAE Systems
The Right Way To Do Exchange In The Cloud
Sponsored by BAE Systems
The Business Value Of Managed Security Services
Sponsored by ThreatConnect
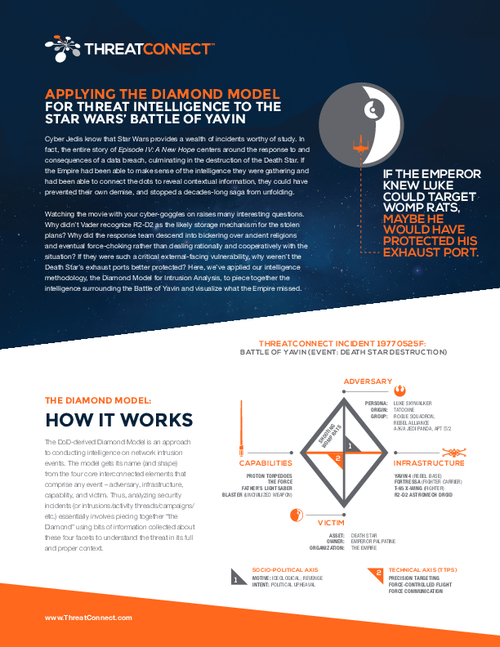
Applying Threat Intelligence to the Star Wars' Battle of Yavin
Sponsored by ThreatConnect