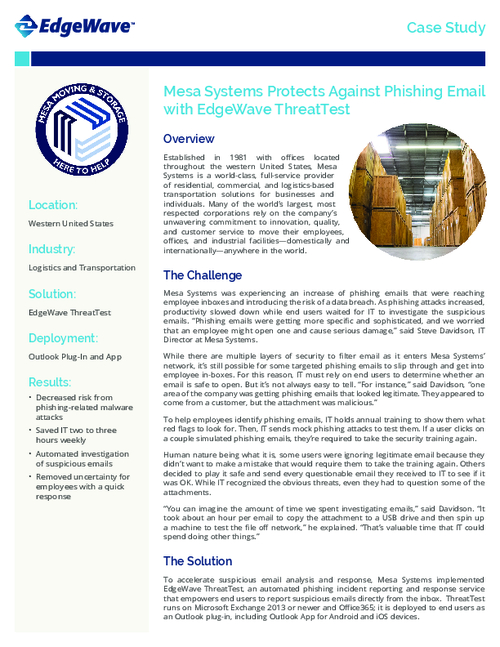
Sponsored by EdgeWave
Sponsored by EdgeWave
Phishing Thrives During Rising Tide of Cybersecurity Threats
Sponsored by Docker
Protection Against Application Security Pitfalls
Sponsored by VMware
2018 Networking and Security Trends Report
Sponsored by Symantec
2018 Gartner Magic Quadrant for Endpoint Protection Platforms
Sponsored by Symantec
2018 India Internet Security Threat Report
Sponsored by Splunk
Investigation or Exasperation? The State of Security Operations
Sponsored by SparkPost
Email's Need For The Security Advantages of Cloud Infrastructure
Sponsored by SparkPost
Securing Email in the Digital Transformation Era
Sponsored by SparkPost
The Product Manager's Guide to Email: How to Build a Successful Growing App
Sponsored by SparkPost
The Product Manager's Guide: How Successful Teams Drive Product, Business, and Career Growth
Sponsored by Acronis
How Protected Is Your Organization Against Ransomware Threats? (German Language)
Sponsored by Acronis
Technology Solutions: Friend or Foe To The Auto Industry? (German Language)
Sponsored by Arctic Wolf Networks