Sponsored by IBM
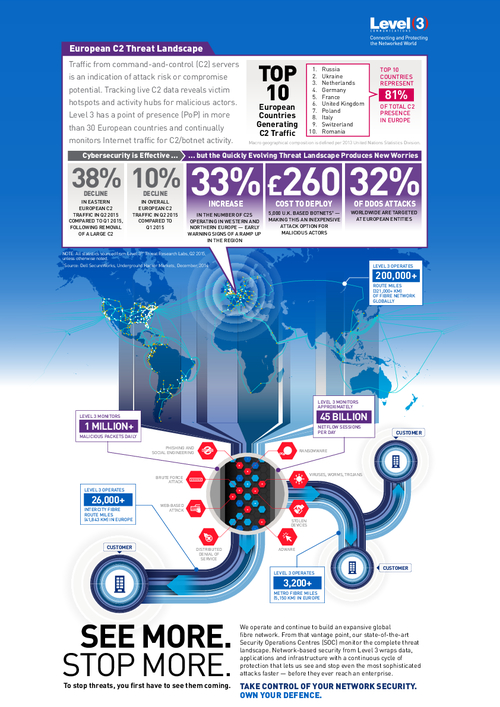
Sponsored by Level 3
Quickly Evolving European C2 Threat Landscape Produces New Worries
Sponsored by Level 3
Improve Your Cyber Security Posture with Secure Pipes
Sponsored by Check Point
The Dangers of Unknown Malware
Sponsored by Check Point
It's Time to Rethink Security Management: A Resource for the Security Professional
Sponsored by VMWare
Extend Security and Control from the Data Center Edge to the Core
Sponsored by VMWare
A New Approach to Data Center Security
Sponsored by VMWare
Seven Reasons Why Micro-Segmentation is Powerful to Have and Painless to Add
Sponsored by VMWare
Micro-Segmentation Builds Security Into Your Data Center's DNA
Sponsored by Solutionary
The Global State of Threat Intelligence
Sponsored by IBM MaaS360
Mobile: The New Hackers' Playground
Sponsored by IBM MaaS360
When App Is The Business, The Business Is The App
Sponsored by Intel Security
Magic Quadrant for Enterprise Data Loss Prevention
Sponsored by Intel Security