Sponsored by ZixCorp
Sponsored by HP
Work Smarter, Not Harder, to Secure Your Applications
Sponsored by Cisco
Next-Generation Firewalls for SMBs
Sponsored by Cisco
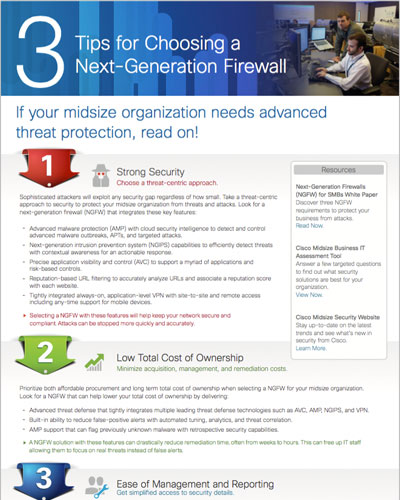
Infographic: 3 Tips for Choosing a Next-Generation Firewall
Sponsored by Cisco
Addressing the Full Attack Continuum: Before, During, and After an Attack
Sponsored by Cisco
2015 Midyear Security Report
Sponsored by StratoKey
Intelligent Cloud Data Protection
Sponsored by Return Path
Healthcare Company Emails Are Putting Customers At Risk-What You Can Do To Stop It.
Sponsored by SurfWatch Labs
How Credit Unions Can Use Cyber Risk Intelligence to Reduce Risk and Improve Efficiency
Sponsored by Zscaler
Forrester Research: SaaS Web Content Security 2015
Sponsored by Zscaler
Enterprise Security: Focusing Protection on Your Employees
Sponsored by Zscaler
What Does the Cloud Mean to Enterprise Security?
Sponsored by Zscaler
APT: The Best Defense Is a Full Spectrum Offense
Sponsored by Proofpoint