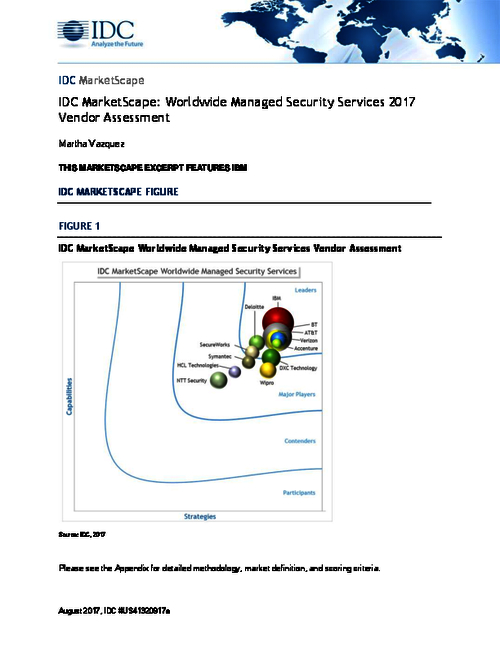
Sponsored by IBM
Sponsored by LogRhythm
Gartner Magic Quadrant SIEM Report
Sponsored by LogRhythm
How to Build a SOC with Limited Resources
Sponsored by Harland Clarke
Aligning PCI DSS Requirements With Risk Management
Sponsored by Harland Clarke
An Enterprise-Wide, Unified Approach to Governance, Risk & Compliance
Sponsored by Harland Clarke
Five Reasons Why The Cloud Is The Right Deployment Option
Sponsored by Bugcrowd
How the Financial Services Industry is Staying a Step Ahead of Cyberattacks in 2018
Sponsored by Bugcrowd
Overcoming the Unique Challenges Security Vendors Face in 2018
Sponsored by Bugcrowd
What Motivates a Bug Hunter: What's In It For Them?
Sponsored by Certified Security Solutions (CSS)
Scalability - A Look at Securely Managing 500 Million Connected Vehicles
Sponsored by VMware
How to Avoid Desktop and App Virtulization Pitfalls
Sponsored by Splunk
Risk Management Framework: Assessing and Monitoring NIST 800-53 Controls for DoD
Sponsored by Tata Communications
The Evolving MECA Cybersecurity Landscape
Sponsored by ValiMail