Sponsored by ThreatTrack
Sponsored by Optum
Healthcare Cybersecurity: The New Strategy
Sponsored by SolarWinds
Data Breach Risk Brief
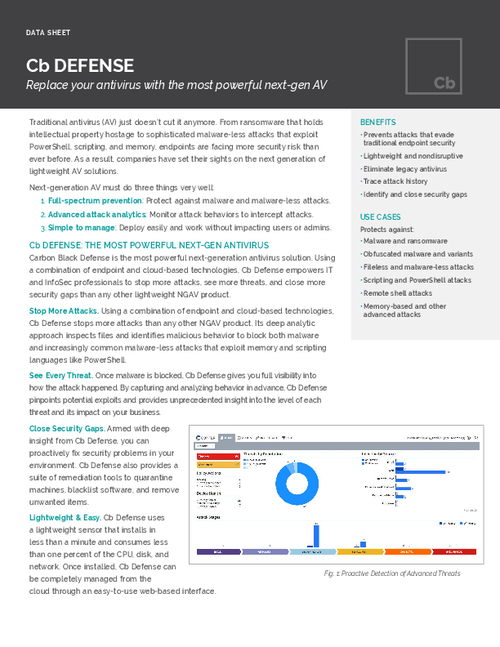
Sponsored by Carbon Black
Replace Your Antivirus with the Most Powerful Next-gen AV
Sponsored by VMWare
Future-Proofing: How to Stay One Step Ahead of Threats to Your Data Center
Sponsored by VMWare
Why Micro-segmentation Matters Now
Sponsored by VMWare
Extend Security and Control from the Data Center Edge to the Core
Sponsored by VMWare
Micro-Segmentation Builds Security Into Your Data Center's DNA
Sponsored by VMWare
Seven Reasons Why Micro-Segmentation is Powerful to Have and Painless to Add
Sponsored by VMWare
A New Approach to Data Center Security
Sponsored by Agari
Understanding Social Engineering
Sponsored by Verisign
Achieving Resilient Cybersecurity
Sponsored by ClearDATA
Protect Your Patient Data While Predicting Threats
Sponsored by Tenable
From Vulnerability Assessment to Continuous Network Monitoring
Sponsored by Malwarebytes