Sponsored by Akamai
Sponsored by iovation
Decentralizing MFA Architecture: Drawbacks and Benefits
Sponsored by Micro Focus
7 Habits to Develop to Increase Your DevOps Success
Sponsored by Micro Focus
Process or Speed? Why You Need Both to Make DevOps Work
Sponsored by Micro Focus
Top C-Level Challenges and Concerns
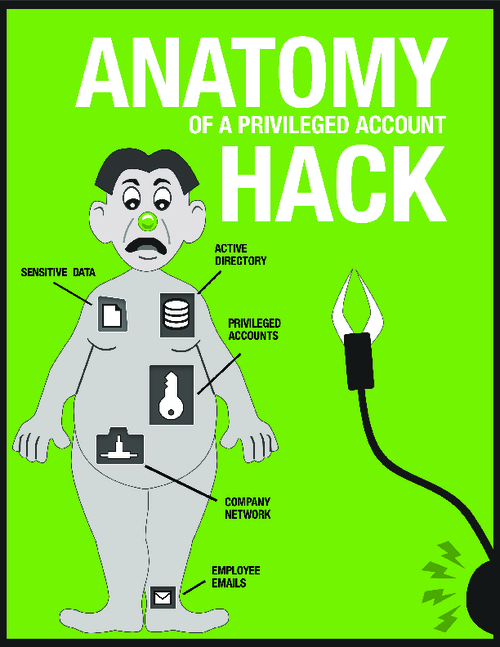
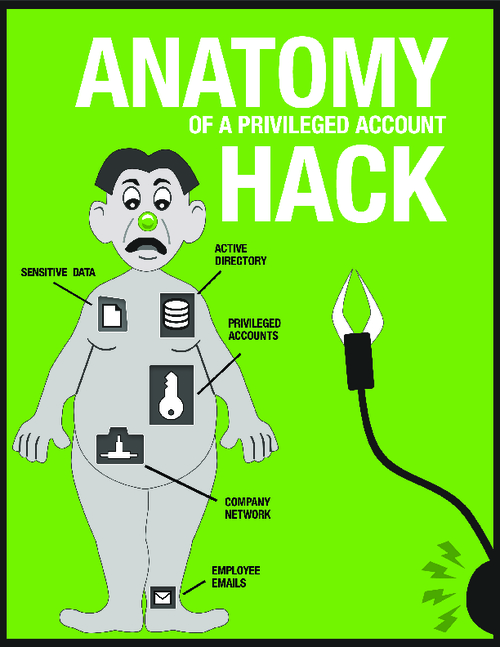
Sponsored by Thycotic
The Anatomy of a Privileged Account Hack
Sponsored by Thycotic
Why Are Hackers so Successful at Targeting Privileged Accounts?
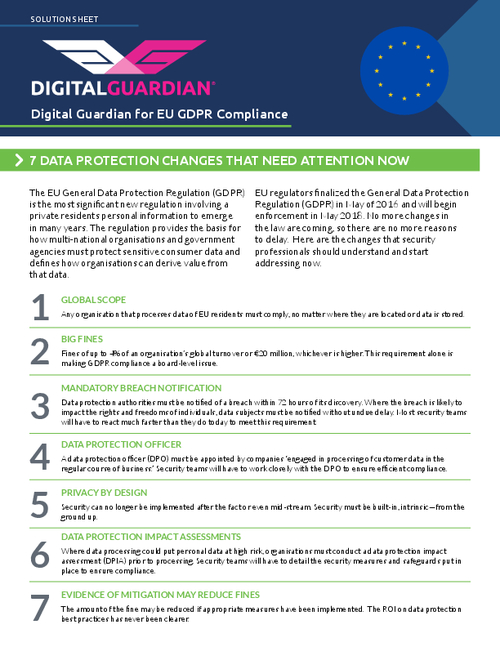
Sponsored by Digital Guardian
A Practical Approach to GDPR Compliance
Sponsored by Digital Guardian
GDPR Compliance Requires Data Loss Prevention
Sponsored by VASCO
Securing Mobile Banking Apps
Sponsored by Venafi
Dark Web Research: Criminals Pay Top Dollar for Your Certificates
Sponsored by BitSight
Making Risk Management More Effective with Security Ratings
Sponsored by BitSight
5 Ways Your Vendor Risk Management Leaves You In The Dark
Sponsored by BitSight
Reporting Cybersecurity to the Board: A CISO's Go-To Guide
Sponsored by BitSight