Sponsored by PhishMe
Sponsored by IBM
The IT Trifecta: Secure, Compliant, and Well-Managed
Sponsored by IBM
The Business Value of Security Monitoring and Analytics
Sponsored by IBM
Transparently Detecting New Account Fraud
Sponsored by Digital Guardian
Real-Time Incident Response
Sponsored by Digital Guardian
The New 2017 Gartner Magic Quadrant for Enterprise Data Loss Prevention
Sponsored by IBM
How to Use Investigative Analysis to Combat Threat Activity
Sponsored by IBM
Enterprise Insight Analysis for Cyber Threat Hunting
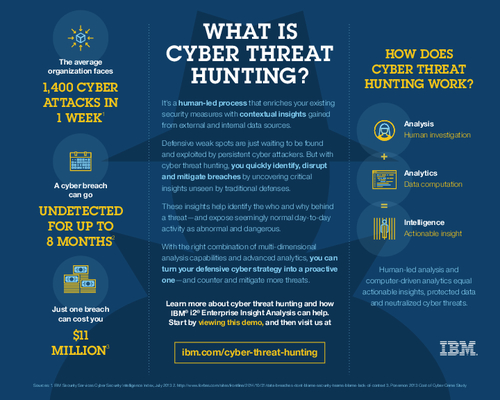
Sponsored by IBM
How Does Cyber Threat Hunting Work?
Sponsored by IBM
Fraud Prevention & Machine Learning
Sponsored by IBM
How to Detect Digital Identity Fraud
Sponsored by IBM
Concepts of Intelligence Operations: The New Approach
Sponsored by IBM
PSD2: The Next Big Opportunity
Sponsored by IBM
Threat Intelligence Case Studies
Sponsored by IBM