Sponsored by Illusive Networks
Sponsored by Illusive Networks
A Deception Approach to Protecting ATM Networks
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Financial Services
Sponsored by Illusive Networks
Three Use Cases for Deception Technology in Healthcare
Sponsored by Cyxtera Technologies
The Power of AI and ML to Fight Fraud
Sponsored by Palo Alto Networks
The CISO Definitive Guide for Picking the NGFW That Works for You
Sponsored by Palo Alto Networks
Reducing the Business Risks of Cyberthreats
Sponsored by Palo Alto Networks
Securely Enabling Cloud Adoption
Sponsored by Ping Identity
The Power of Identity in Financial Services
Sponsored by Sift Science
E-Commerce's Guide To Stopping Content Abuse Before It Happens
Sponsored by Sift Science
E-Commerce & The Future of Fraud Fighting
Sponsored by Sift Science
The Retail Industry's Complete Guide To Preventing Account Takeover
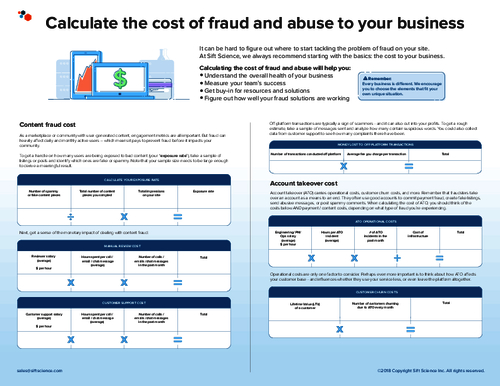
Sponsored by Sift Science
Calculating The Cost of Fraud and Abuse to Your Business
Sponsored by Sift Science
Complete Guide To Preventing Account Takeover
Sponsored by Sift Science