Sponsored by 817
Sponsored by Trusteer
Mobility on Hold: Get Back on Track with Mobile Risk Mitigation
Sponsored by Webroot
The Wild, Wild West of Mobile Apps
Sponsored by Webroot
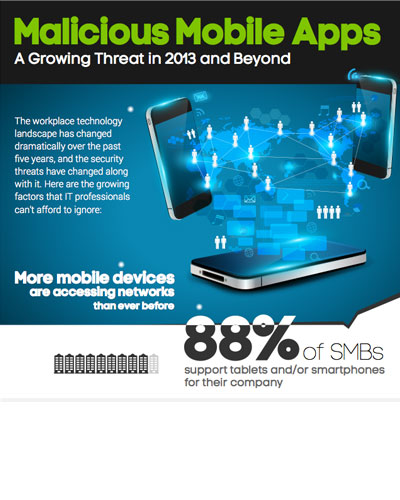
Malicious Mobile Apps: A Growing Threat in 2013 and Beyond
Sponsored by Webroot
Mobile Browsing - Is Your Company at Risk?
Sponsored by HP
Top Three Mobile Application Threats
Sponsored by Accellion
BYOD File Sharing - Go Private Cloud to Mitigate Data Risks
Sponsored by Accellion
5 Best Practices for Secure Enterprise Content Mobility
Sponsored by Accellion
Strategy for Securing Mobile Content: 5 Key Guidelines
Sponsored by Accellion
Mobilize SharePoint Securely: Top 5 Enterprise Requirements
Sponsored by Accellion
Raising the Bar in Secure Cloud-Based File Sharing
Sponsored by Good Technology
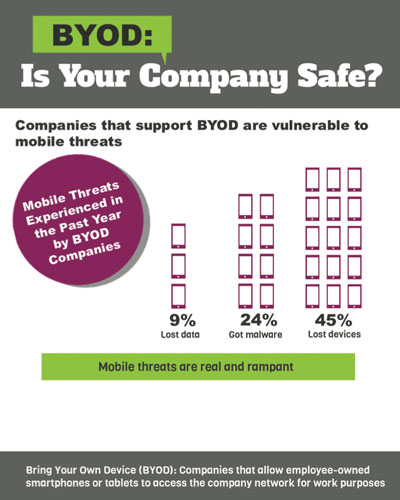
Together at Last - BYOD and Solid Security
Sponsored by Good Technology
Effective Identity and Access Management in a Mobile World
Sponsored by Good Technology