Blockchain & Cryptocurrency , Incident & Breach Response , Managed Detection & Response (MDR)
TeamTNT Deploys Malicious Docker Image on Docker Hub
Threat Actors Use Scanning Tools for Malicious Activities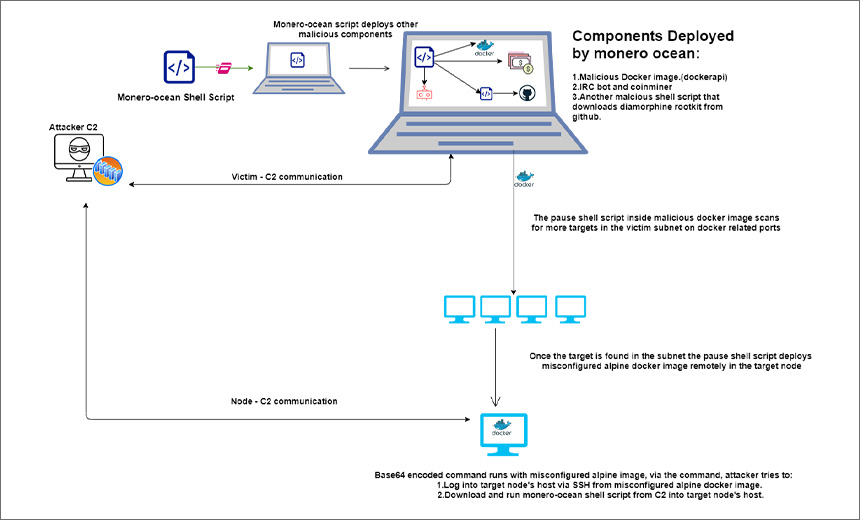
Researchers at Uptycs Threat Research have uncovered a campaign in which the cloud-focused cryptojacking group TeamTNT is deploying malicious container images hosted on Docker Hub with an embedded script to download testing tools used for banner grabbing and port scanning.
See Also: 2018 Threat Landscape Report
Researchers identified the Zgrab scanner penetration testing tool, which is used for banner grabbing, and the masscanner penetration testing tool, which is used for port scanning.
The researchers found that threat actors scan for targets in the victim’s subnet and perform malicious activities using the scanning tools inside the malicious Docker image.
Docker is a popular platform-as-a-service container offering for Linux and Windows devices that developers use to help develop and package applications.
Attack Analysis
"Criminal groups continue to target Docker Hub, GitHub, and other shared repositories by using container images and software components that include malicious scripts and tools. They often aim to spread coinminer malware, hijacking the computing resources of victims to mine cryptocurrency," according to Siddharth Sharma, a malware researcher at Uptycs.
The Uptycs researchers found that the malicious Docker image was hosted in Docker Hub under the name alpineos, a community user who joined Docker Hub on May 26, 2021. At the time their research was published, alpineos’ profile was hosting 25 Docker images.
While analyzing the Dockerapi image, researchers uncovered 5,400 downloads within approximately two weeks of the image being added. The researchers say, "Another Docker image from the repositor, ‘basicxmr’ has been downloaded more than 100,000 times. This clearly suggests that the profile is actively developing malicious images."
The Uptycs Threat Research Team reported the Docker image hosted in the Docker Hub website to the security team on Sept. 30, 2021.
Group TeamTNT
The cloud-focused cryptojacking group TeamTNT is known for targeting Amazon Web Services credential files on compromised cloud systems to mine for the cryptocurrency Monero. Security researchers first spotted the group in 2020.
The group has been scanning for and compromising Kubernetes clusters in the wild, according to a Trend Micro report. In previous research, Trend Micro noted that TeamTNT was actively stealing AWS, Docker and Linux Secure Shell credentials and waging cryptojacking attacks and placing backdoors - such as IRC bots and remote shells - inside Linux devices.
The Trend Micro researchers also observed that most of the compromised nodes identified in internet service providers and cloud service providers were in China and the U.S.
"TeamTNT is a well-known threat actor which targets *nix based systems and misconfigured Docker container environments. Threat actors associated with TeamTNT mostly use open-source tools in their campaigns, such as XMrig miner, Tsunami IRC bot (a.k.a kaiten) and the diamorphine rootkit," the researchers note.
Attack Chain
The researchers found that the threat actors had deployed a new malicious Docker image named Dockerapi, which was hosted on Docker hub website.
"Using Docker, the malicious image was run with the privilege flag, and was mounted with the victim host and victim host’s network configuration. The malicious Docker image had an embedded shell script named 'pause,'" the researchers say. "The 'pause' shell script inside the malicious Docker image had commands to install masscanner and the zgrab tool."
Upon setting up the scanning tools, the functions in the script scan the victim subnet on Docker-related ports for more target virtual machines, or nodes.
Once a target node is identified, the "pause" shell script runs the misconfigured alpine Docker image remotely from the victim machine in the target node, passing a base64 command as the command line.
The command generates the ssh key and adds it to the authorized_keys file, which logs into the target node’s host via ssh and downloads the monero-ocean shell script from the C2 into the target node’s host.
"The monero-ocean shell script in this campaign deploys Xmrig miner and the Tsunami IRC bot on the system it is being run on. The monero-ocean shell script also downloads another shell script (diamorphine shell script) which downloads and deploys the diamorphine rootkit to the victim’s system. The diamorphine rootkit consists of features such as hiding the pid, syscall table hooking and giving root privilege to the pid," the researchers say.
"Using the command Docker ps, we can identify the malicious Docker image runs pause shell script. The pause shell script inside Docker image installs basic utilities and the scanning tools Zgrab and masscan. Upon installation of these tools, commands inside the pause shell script start heavy scanning on Docker related ports in an attempt to target more nodes (machines) in the victim subnet," they note.
Many services nowadays run in isolated Docker containers so, to maintain a robust security stance, it is crucial to be able to detect malicious images early in the CI/CD pipeline as well as monitor all the container activities in runtime, the researchers say.