Steps Executives Can Take to Fight Fraud
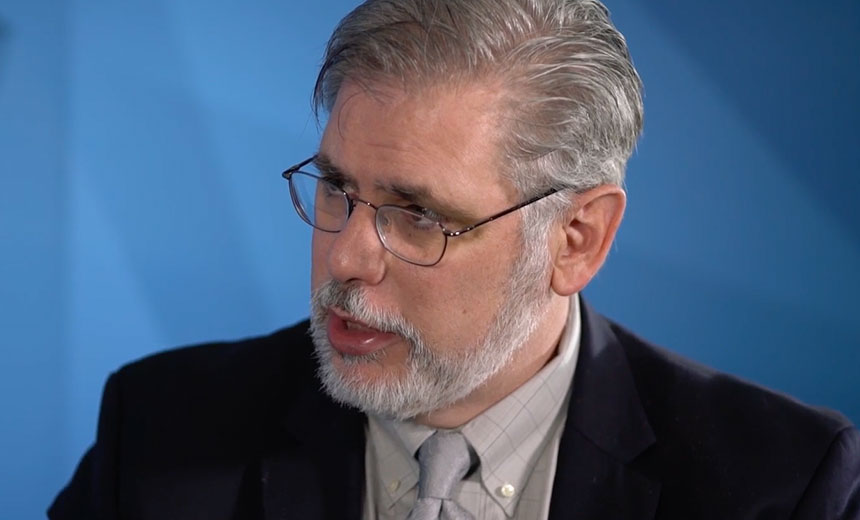
Security Expert Chuck Easttom on Using Caution on Social MediaTo minimize the risk of business email compromise schemes and similar types of fraud, senior executives at businesses should avoid posting information about their activities on social media and other accessible forums, says security expert Chuck Easttom.
See Also: The State of Ransomware Readiness 2022
Business email compromise exploits use well-thought-out socially engineered scams, often involving impersonating executives, that con unsuspecting accounting staff members at businesses into scheduling fraudulent wire transfers.
In a video interview at Information Security Media Group's 2015 Fraud and Data Breach Prevention and Response Summit Dallas, Easttom describes how organizations get suckered by phony emails. "If you get a general email that says 'Dear sir or madam,' you probably dismiss it immediately. If you get an email that calls you by name and references things like, 'I saw you at the conference last Wednesday morning,' well, you were at a conference last Wednesday. That seems legitimate," Easttom says.
Easttom urges financial institutions to consider keeping certain information about senior executives less accessible to the public, similar to how intelligence and military agencies handle information. "[Recently], the secretary of Department of Homeland Security visited Cuba. It was announced once he was in Cuba. It was not announced before he flew for security reasons," he says.
"If I know that the vice president of finance is on a cruise for 10 days, then he's the guy I want to spoof. If you're a senior official at a bank, don't tell everyone you're about to be in Hong Kong for a summit. Tell everyone the week after how much you enjoyed the summit."
In this interview, Easttom also discusses:
- How "money mules" are used to lure banks into thinking that fraudulent transfers are legitimate;
- Why an honest assessment of security processes is the most important thing to do after a breach; and
- Why a breach's impact can be continuous.
Easttom, an independent consultant, is a computer security expert with more than 20 years of experience and multiple certifications, including CISSP, ISSAP, CEH, MCT and CCFP. In addition, he has published 19 books, including computer security textbooks used at universities around the world. He holds six patents and conducts training in security for law enforcement, federal agencies and other governments.