Events , Governance & Risk Management , Incident & Breach Response
Stepping Up to Meet Advanced Threats
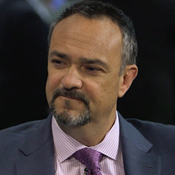
BH Global's Soh on the Need to Improve Incident Response
Most enterprises across verticals in Asia are prone to advanced threats due to an acute lack of security awareness, says Ken Soh, CIO and director of e-strategies at BH Global, a provider of supply chain management, design and manufacturing and engineering services to the oil and gas industry. This lack of awareness has only resulted in an increase in security risks and vulnerabilities.
See Also: Digital Evolution and Fraud Evolution: How to Keep Up with the Changing Times
To make up for this deficit, Soh says, "The foremost imperative need for enterprises is to have an incident response mechanism in place that can help detect and pre-empt attacks."
Soh finds increasing security risks enveloping enterprises in the Asia Pacific region because of a surge in sophisticated cyber-attacks. "With the increase in labor cost, companies have been increasingly relying on automation and remote monitoring, which increases the chance of compromising security," he says.
One way to address the risk, he says, is to convince boards of directors to enable security heads to have a critical response team in place to detect and pre-empt attacks. "A holistic approach is needed to get the board to appreciate the importance of security," he says.
In this interview with Information Security Media Group, conducted at the RSA Conference Asia Pacific and Japan in Singapore, Soh raises concerns around enterprises' lackadaisical approach toward deploying cybersecurity and IT security solutions in combating advanced threats. He outlines the importance of convincing the board to invest in security and enabling teams to deploy solutions to prevent and detect cyberthreats. Soh also discusses:
- Focusing on innovations to tackle security challenges;
- Risk vectors surrounding enterprises;
- Best security practices to improve security postures.
In addition to his role as CIO and director of e-strategies at BH Global, Soh is CEO of the company's Athena Dynamics subsidiary. Previously, he worked at Temasek Polytechnic, NCS and Singapore Computer Systems Ltd.
Advanced Threats
GEETHA NANDIKOTKUR: What kind of security risks envelop enterprises from the Asia Pacific region?
KEN SOH: Most enterprises, including transportation, energy, water supply systems and marine engineering, across the Asia Pacific region face cyberattacks, which are now presenting a greater risk to enterprises and their infrastructure. Enterprise IT security risk is another challenge. The reason: with the increase in labor cost, companies increasingly rely on automation and remote monitoring, which increases chances of compromising security. As per a research report, it is estimated that cyberattacks against oil and gas infrastructure and shipping alone will cost companies close to $1.9 billion by 2018.
Various research reports have discovered significant holes in key technologies used in navigation, tracking, encryption and systems control. Enterprises are prone to malware attacks, which are advanced and multi-faceted, commonly named advanced threats, which include malware that could sit silently in the infected PC and act as an agent for a remote command and control station, which can then steal or manipulate information in the infected PC remotely, even from another part of the globe.
The other challenges around people, process and technology are undergoing major transformation. The people factor is most complicated, as they are against change management. The processes are outdated - it's not easy to bring in new change. Technology's getting dynamic with new jargon hitting the market very rapidly. Besides technical, reputational and operational risks, organizations are vulnerable to new forms of attack.
Convincing the Board
NANDIKOTKUR: How do security leaders involve stakeholders in convincing board members about the risk situation?
SOH: As compared to the past, it's easy now to convince board members about threats and breaches, thanks to the breaches experienced by top enterprises in the recent past, which have drawn attention from the board. But not much momentum is witnessed in deploying risk frameworks within organizations, as complacency still exists. However, it's imperative to get the board to understand that protecting the operational, reputational risk of the organization is of paramount importance to prevent suffering the aftermath of attacks. It's crucial to convince them to have a critical response team in place to detect and pre-empt attacks, rather than just react. A holistic approach is needed to have the board appreciate the importance of security.
Security Innovations
NANDIKOTKUR: What are the current security innovations for tackling these challenges?
SOH: While signature-based sandboxing is being used by most enterprises, much needs to be done in addressing APT malware challenges. I believe that all the stakeholders must encourage use of a pre-zero day attacks draft framework for disaster risk reduction. Innovations could be in the form of strengthening governance and institutions to manage disaster risk and invest in building economic, social, cultural and environmental resilience to combat cyberthreats. It again relates to aligning people, processes and technology in enhancing preparedness for effective incident response mechanism.
Best Practices
NANDIKOTKUR: What kind of security best practices are necessary to make enterprises cyber safe?
SOH: It must be a holistic approach with the primary task of deploying identity-based solutions to prevent malware from intruding into the system. Security practitioners must understand business pain points. As a CIO, I understand how managements are not sensitive to spending enough on security, which is always measured in terms of ROI. It's critical to hire the right teams to address security. Most often, enterprises think having a SoC [Security Operations Centre] is sufficient to address organizational risk challenges; that's a false notion. The security could be at the application development and coding level, which is often overlooked. As a best practice, it's imperative for IT and security teams to tighten security at the application layer and prepare effective SLAs with vendors.
Additional Summit Insight:
Hear from more industry influencers, earn CPE credits, and network with leaders of technology at our global events. Learn more at our Fraud & Breach Prevention Events site.