Incident & Breach Response , Managed Detection & Response (MDR) , Security Operations
SolarWinds Breach Response: 'Shields Up'
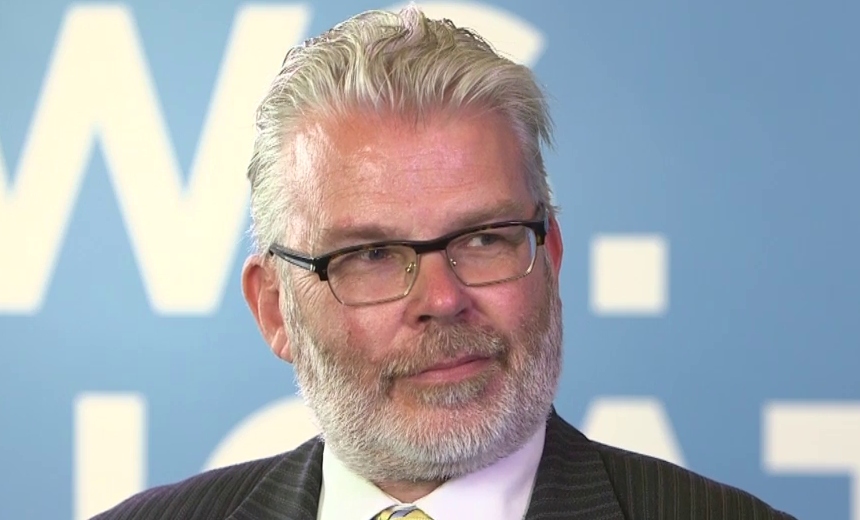
Ex-Federal CISO Gregory Touhill on the Need for Improving Cyber Deterrence StrategyHe was the first U.S. federal CISO, and before that he was an Air Force general. So when Gregory Touhill reacts to the coordinated supply chain attack on SolarWinds, he does so in military terms. His message to the global cybersecurity community: “Shields up.”
See Also: Demystifying Managed Detection and Response Services
Touhill, now president of Appgate Federal, says this breach is a call to arms. “We need to be looking for further activity – not only in IT, but in operational technology, industrial controls systems and, arguably, in the code that is running a lot of our internet of things devices.”
In this video interview with Information Security Media Group, Touhill discusses:
- The potential scale of this supply chain attack;
- Lessons to learn from this campaign;
- Why this incident calls for “a more credible cyber deterrent strategy.”
Touhill was selected by President Obama as the U.S. government's first CISO. His other civilian government service includes duties as the deputy assistant secretary for cybersecurity and communications in the U.S. Department of Homeland Security and as director of the National Cybersecurity and Communications Integration Center, where he led national programs to protect the United States and its critical infrastructure. Touhill is a retired Air Force general officer, a highly decorated combat leader, an accomplished author, a former American diplomat and a senior executive with documented high levels of success on the battlefield and in the boardroom.