Fraud Management & Cybercrime , Ransomware
Shade Ransomware Operation Apparently Shuts Down
Those Claiming to Be Operators Say They've Released 750,000 Decryption Keys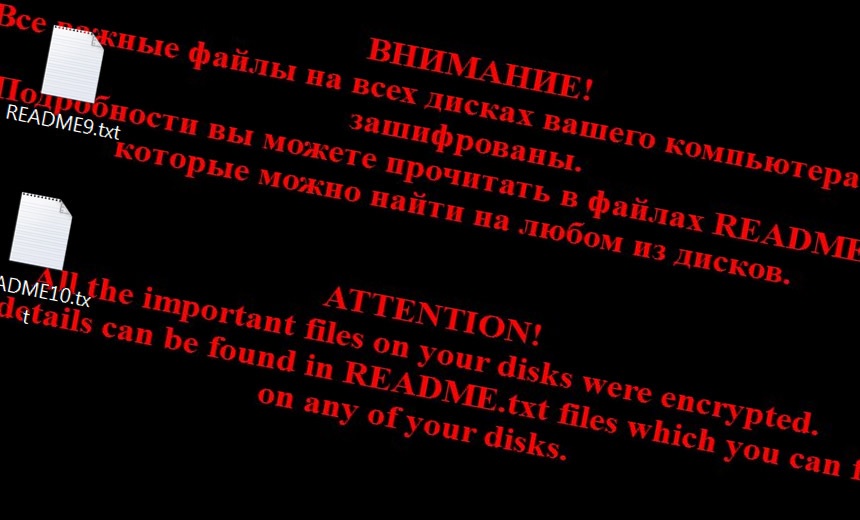
Those claiming to be operators of the Shade ransomware strain say they have closed down their operation and have released more than 750,000 decryption keys, according to a message posted on GitHub.
After the GitHub message was posted, Sergey Golovanov, a security researcher with Kaspersky, posted on Twitter that the decryption keys appeared to be genuine.
See Also: The Gorilla Guide to Modern Data Protection
But Jornt van der Wiel, another security researcher at Kaspersky, notes that even though the decryption keys are real, the true motive behind why the Shade operators decided to end their operations may never be known.
"Keys can be stolen by a rival gang who put the message on Github, or it can be the real authors," van der Wiel tells Information Security Media Group. "We will never know until law enforcement agencies do some arrests."
Those who say they are the operators of Shade, which is also known as Troldesh or Encoder.858, say in their GitHub post that they shut down their operations at the end of 2019 and that they were publishing their decryption keys, which can help security companies create their own tools to help remove the malware and recover any other crypto-locked files.
"We are also publishing our decryption [software]; we also hope that, having the keys, anti-virus companies will issue their own more user-friendly decryption tools. All other data related to our activity (including the source codes of the Trojan) was irrevocably destroyed," according to the GitHub post. "We apologize to all the victims of the Trojan and hope that the keys we published will help them to recover their data."
Rise and Fall of Shade
First spotted in 2014, Shade was one of the longest-running ransomware strains, mainly targeting victims in Russia. But security researchers spotted ransom notes in English as well (see: Ransomware Analysis: 'Shade' Surges; Other Trends Emerge).
In the first half of 2019, security firm Group-IB calculated that Shade was the most prevalent strain of malware, accounting for 53 percent of all malicious code spotted in the wild. One reason why is that in addition to launching ransomware attacks, Shade could mine for cryptocurrency and create phony web traffic for ad fraud campaigns.
By the end of the 2019, however, other ransomware, such as Maze and Sodinokibi, become more prevalent, and the gangs behind those began publishing data when ransom demands were not met (see: More Ransomware Gangs Join Data-Leaking Cult).
Managing Editor Scott Ferguson contributed to this report.