Governance & Risk Management , IT Risk Management , Privacy
Service Provider to Government Left Database Exposed
Granicus Says Risks Involved Were Low
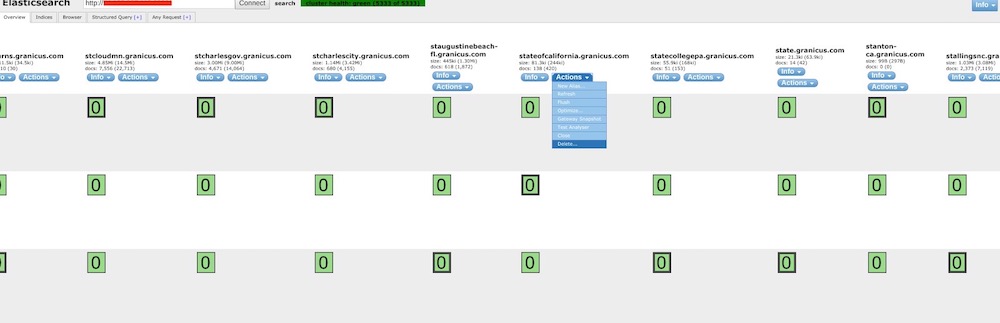
Granicus, one of the largest IT service providers for U.S. federal and local government agencies, acknowledges that it left a massive Elasticsearch database exposed to the internet for at least five months, but it says the risks involved were low.
See Also: The Biggest & Boldest Data Breaches & Insider Threats of 2023
Denver-based Granicus provides a range of cloud-based services for government agencies, including website design, email and social media outreach as well as public records management. It’s owned by the private equity firm Vista Equity Partners, and it has clients across the U.S., Canada and Europe, including in the U.K. According to Granicus' website, the company has more than 4,500 public sector customers.
The database, Granicus says, was only used to index links on the websites of its public sector customers, allowing for faster searches. The links all led to public, nonsensitive data, the company says.
Elasticsearch is an open-source platform for storing and querying data, If it's rolled out in a misconfigured manner, the data it stores may be left internet-accessible to others.
Researcher’s Discovery
The internet-exposed database was discovered by Dan Ehrlich, an Austin, Texas-based researcher who runs the consultancy Twelve Security. Ehrlich has previously found exposed databases tied to IoT security camera maker Wyze and an Android app called Peekaboo Moments (see: Baby's First Data Breach: App Exposes Baby Photos, Videos and Smart Home Device Maker Wyze Exposed Camera Database ).
The database, which is now offline, was a three-node cluster hosted on Amazon Web Services, with cluster names such as "us-production-1," Ehrlich says. It ran an outdated version of Elasticsearch, version 0.90.13, which was released in March 2014, he adds. The current version is 7.6.0.
Ehrlich says the Granicus database included links to files on websites belonging to the Department of Health and Human Services and U.S. House of Representatives, as well as hundreds of other local government units across the country. The database also contained links to files published by more than 1,700 Granicus customers, the researcher says.
Because the database's permissions were open, Ehrlich says anyone who could have accessed the database could have written or modified data. Ehrlich originally thought that changing links within the database would mean the changes would also show up on Granicus’s clients’ websites. But that would not have been possible, Gerry Hansen, Granicus' vice president of cloud and its data protection officer, tells Information Security Media Group.
Hansen says the Elasticsearch database that was temporarily exposed accepts changes written to it but does not push them back to the corresponding websites. He says the database is used for an internal search feature that Granicus' customers use. But the exposed database is not used for the search boxes on government websites, he says.
Troy Hunt, a data breach expert and creator of the Have I Been Pwned breach notification website, says that even if the Elasticsearch database didn’t write back to a production database, whomever was using the internal search feature could be at risk if the links in the exposed Elasticsearch database were changed to malicious ones.
“Data is usually stored so that it can be retrieved and redisplayed,” Hunt says. “If it’s displayed to anyone who then could click on a malicious link, it’s possible they’d be hit with malware.”
In a statement provided to ISMG, Granicus appeared to acknowledged the risk outlined by Hunt but said the exposure would have been limited.
“The search function in question was the result of a custom API integration that was available to only a very small number of customers," Granicus says. "A misconfiguration in this server made it possible to edit those links, and we acted swiftly to ensure the issues were addressed without incident. We have determined that this misconfiguration did not cause any other exposure to our customers and that the issue has since been resolved.”
But running an outdated version of Elasticsearch – in this case, version 0.90.13 – could pose other risks, says Cooper Quintin, senior staff technologist with the Electronic Frontier Foundation. Quintin says there are known remote code execution vulnerabilities, such as CVE-2015-5377, that affect Elasticsearch.
“In addition to leaving this database open, they [Granicus] put themselves at further unnecessary risk by running such an old [Elasticsearch] version with potential remote code execution vulnerabilities,” Quintin says.
Finding Exposed Databases
It's unknown whether anyone else, besides Ehrlich, accessed the temporarily exposed database. Finding these types of exposed Elasticsearch databases is relatively easy, thanks to specialized search engines such as Shodan and BinaryEdge.
Ehrlich says he found something suspicious in one part of the database: a "type" field that reads "howtogetmydataback." Older versions of Elasticsearch included a “_type" field that was used to help make data searches faster, although the feature has been deprecated.
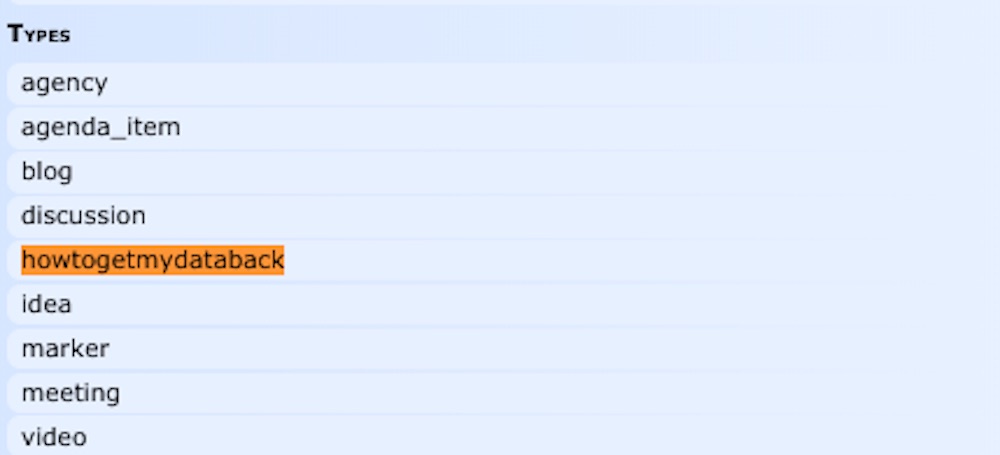
Ransomware operators have been known to leave notes in databases such as MongoDB and others in order to alert victims that they've been compromised. Bleeping Computer reported in May 2019 that the same wording – “howtogetmydataback” was found in the “type” field of an unsecured Elasticsearch database belonging to SkyMed, a medical evacuation service.
Rapid Growth
Over the last few years, Granicus has grown through a series of acquisitions.
Granicus had about 1,200 public sector clients until 2016, when it acquired GovDelivery, another public sector technology provider, which served 1,800 clients. It has acquired other smaller providers as well.
Have I Been Pwned's Hunt says the cloud has complicated organizations' ability to keep track of their IT assets, particularly when acquiring other companies. The firms being acquired may not have good inventories of what they're running, he says.
"I'm sympathetic to organizations that have a large number of assets out there, but they are accountable as well," Hunt says.