Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering
Russian a Suspect in German Parliament Hack: Report
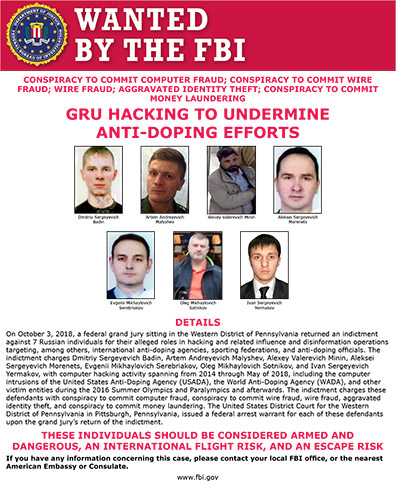
Alleged GRU Agent Charged Earlier in Connection With U.S. Election Interference
German prosecutors now believe that an alleged Russian hacker who apparently is a member of an elite military unit is responsible for the 2015 cyberattack against Germany's parliament, which included the theft of thousands of emails, according to a report in the newspaper Sueddeutsche Zeitung.
This week, the German attorney general's office obtained an international arrest warrant for Dmitriy Sergeyevich Badin, a 29-year-old Russian national who is suspected of hacking the network of the country's parliament five years ago, according to the newspaper. The warrant has not been made public and prosecutors have made no official statement.
Badin is suspected of serving in an elite cyber espionage unit – Unit 26165 - of the Russian Main Intelligence Directorate. Commonly referred to as the GRU, the directorate serves as the military intelligence division of Russia's armed forces, according to the news report.
Badin and other members of the GRU also are suspected of participating in some of the largest state-sponsored hacking operations in recent years. Badin, along with six other alleged GRU members, was indicted in 2018 by the U.S. Justice Department on various charges related to interference in the U.S. 2016 U.S. presidential election. GRU members are also suspected of hacking of the World Anti-Doping Agency in 2017 and then leaking stolen data (see: Feds Indict 7 Russians for Hacking and Disinformation).
Badin is believed to be living in Russia and is unlikely to be extradited to face charges in another country.
The German attorney general's office could not be immediately reached for comment. A Russian official denied Badin's involvement in the 2015 incident, according to Sueddeutsche Zeitung.
2015 Attack
In May 2015, Germany's lower house of parliament, known as Bundestag, discovered that its PCs and servers had been hacked using malware, with the attackers having gained administrative-level rights for the entire network and infrastructure, according to U.S. and German media reports (see: German Parliament Battles Active Hack)
It's now believed that Russian hackers sent a phishing email to several members of the German parliament with a malicious link portrayed as leading to a United Nations website. The attackers further impersonated the U.N. by using the domain "@un.org" to send the emails, which included subject lines such as: "Ukraine conflict with Russia leaves economy in ruins," according to the Sueddeutsche Zeitung news report.
When a target of the phishing campaign clicked on the link, it installed malware on their device, enabling hackers to gain a foothold within the IT network of the German parliament, according to Sueddeutsche Zeitung. One malware strain used was called "Mimikatz," which can steal passwords.
Federal prosecutors in Germany believe that Badin was personally involved in the hack, according to the news report. Badin allegedly created malware called "VSC.exe" in May 2015 and used it as part of the phishing attack that started around the same time, the newspaper reports.
Data Stolen
On May 11, 2015, a security company that tracks suspicious servers around the world observed that a command-and-control server controlled by the hackers was communicating with two computers in the German parliament, according to Sueddeutsche Zeitung. By the time the attack ended on May 20, 2015, about 16 GB of data containing tens of thousands of emails by members of parliament had been stolen, the newspaper reports.
Over the last five years, Germany's Federal Criminal Police Office worked with the officials from the U.S. and Netherlands to discover the origin of the hack, according to the Sueddeutsche Zeitung report.
GRU Link
In April 2018, four members of the GRU's Unit 26165 were stopped by Dutch counterintelligence agents as they were traveling to The Hague. At the time, Dutch investigators confiscated their luggage, including laptops and cell phones, which provided German authorities with valuable information about the 2015 hack of Parliament as well as the ties to Badin, according to Sueddeutsche Zeitung.
In addition, investigative site Bellingcat claims to have linked Badin to the GRU by using a leaked Moscow car registration database, which included his passport number and registered addresses.
The GRU's Unit 26165, along with another GRU division called Unit 74455, are believed to be part of an state-sponsored advanced persistent threat group known as Fancy Bear, APT28 or Sofacy.
In addition to interfering with the U.S. election in 2016 and hacking the World Anti-Doping Agency in 2017, the APT group is suspected of launching an October 2019 cyberattack on the country of Georgia that crippled at least 2,000 government, news media and court websites (see: US, UK Blame Russia for Cyberattack in Country of Georgia)