3rd Party Risk Management , Cyber Insurance , Cybercrime
Premium Hikes Spur Improved US Cyber Insurance Loss Ratios
Declining Loss Ratios Means Insurance Premium Increases Might Moderate in Late 2022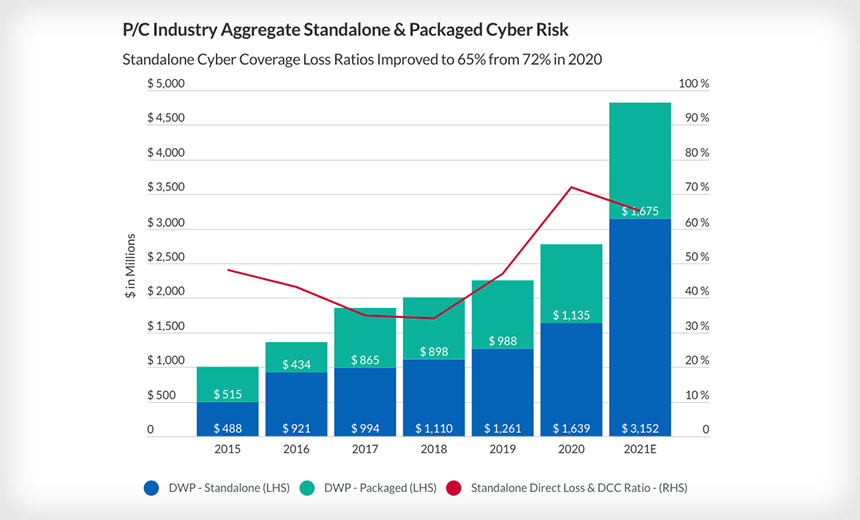
A surprising improvement in loss ratios for cyber insurance providers in 2021 means the rapid rise in premiums might at last subside later this year.
See Also: Take Inventory of Your Medical Device Security Risks
The loss ratio - which tracks claims paid by an insurer versus premiums earned - declined for the first time since 2018 despite the frequency and severity of claims filed for cyberattacks increasing yet again in 2021, Fitch Ratings found. The improvement was due to premium hikes so steep that they exceeded incurred losses as well as more vetting by carriers of businesses seeking insurance coverage.
"I thought this was inevitable," Anthony Dagostino, founder and CEO of cyber insurance provider Converge, tells Information Security Media Group. "The underwriting approach the industry has taken is to get more premiums, ask more questions, and restrict coverage, and that's how you get improved loss ratios. It's a simple math equation at the end of the day in insurance."
Losses are High, But Premiums are Higher
Fitch revealed this week that the cyber insurance loss ratio in the United States declined from 72% in 2020 to 65% in 2021, meaning that for every $100 in premiums the insurance company took in last year, they paid out $65. Still, the cyber insurance loss ratio remains significantly worse that what the industry experienced from 2015 to 2019, when it never rose above 48%, according to Fitch (see: Increase in Ransomware in 2022 Will Kill Cyber Insurance).
A loss ratio below 100% doesn't necessarily mean cyber insurance providers are making money since it only factors in direct claim payouts and doesn't consider the other costs associated with running an insurance company like underwriting fees and legal and adjuster expenses, Gerald Glombicki, senior director at Fitch, tells ISMG.
Given how high indirect costs are in the insurance industry, Glombicki still doesn't think carriers are making money on their cyber policies. Conversely, Dagostino thinks roughly three-quarters of providers are making turning a profit today off cyber insurance, with the unprofitable 25% focused on industries that have been hit particularly hard by cyberattacks in recent months.
The improved loss ratio comes against a backdrop of a 92% increase in premiums for stand-alone cyber companies during 2021, with quarter-over-quarter premium rate hikes jumping from 18% in the first quarter of 2021 to 34.3% in the fourth quarter of last year, Fitch found. In comparison, annual premiums for the property and casualty insurance market as a whole increased by just 9% in 2021, Fitch reported.
To avoid triple-digit premium hikes, some firms are opting for insurance policies that have deductibles of $25,000 rather than $10,000 or settling for reduced policy limits or coverage terms, Glombicki says. This was particularly true for retailers or hospitality companies at the onset of COVID, who were either opting to buy less coverage or not renewing their cyber insurance coverage altogether, Dagostino said.
"In my crystal ball, I think rate increases will continue through 2022 with a little bit of tapering in Q4," Dagostino says. "And then rates will come down in the future barring any big events that happen or systemic risks or new kinds of threats that emerge."
Asking the Right Questions
Cyber hygiene is now central to the insurance underwriting process, Glombicki says, with carriers refusing to cover businesses that don't have multi-factor authentication, aren't securing their endpoints, and don't have an incident response plan in place. Providers have also pushed for cyber resiliency measures like network segmentation to stem the bleeding around incidents involving zero-day flaws.
The cyber insurance industry was historically focused on violations of data breach notification rules such as GDPR and started loss ratios rapidly accelerate as ransomware attacks became more pervasive over the past three years, Glombicki says. Most cyber insurance providers aren't auditing or pen testing policyholders, but want to hear about the measures they're taking to manage their attack surface.
"CISOs are trying to limit their attack surface and limit the impact of an attack and do it in the most cost-effective and user-friendly manner that doesn't unnecessarily inhibit or encroach upon actually running the business," Glombicki says. "They have to take a lot of variables into consideration when they actually formulate their plan."
Insurance carriers want to ensure that customers have controls in place like multi-factor authentication, offline regular backups, micro-segmentation, employee training and awareness, end of life system management, privileged access management, data encryption, an incident response plan, and open remote desktop protocol since these effectively protect against ransomware attacks, Dagostino says.
In response to these questions, Dagostino says there's been an uptick in businesses using multi-factor authentication, backup systems, and either endpoint detection and response or managed detection and response. In addition, early and mid-stage companies that can't afford to build out a Security Operations Center are turning toward managed security service providers rather than tasking the COO with security.
"The questions that insurance companies ask are working," Dagostino says. "And I think for when we see this report for calendar year 2022, I think we'll definitely see an improvement in claims based on the questions that they're asking."
At the same time, a lack of technical expertise around cybersecurity for the major insurance carriers has resulted in forms that have a lot of 'yes/no' questions and don't account for compensating controls. Policy holders with unorthodox security architectures are hurt by the rigid approach to oversight since, for instance, a nursing station at a hospital can't have multi-factor authentication, Dagostino says.
Going forward, Dagostino expects insurers to validate that policyholders have configured their multi-factor authentication and endpoint detection and response correctly rather than simply asking if they've been procured. In addition, he said CISOs should deploy risk quantification tools that leverage claim data to figure out how they'd be impacted by a cyberattack and where they should prioritize investment.
"The process has woken up a lot of companies to invest in security a bit more," Dagostino says. "They're realizing not only will it get them better coverage or bring their premium down a little bit, but it'll avoid them getting a ransomware attack in the first place."