Audit , Data Loss Prevention (DLP) , Encryption & Key Management
Neiman Marcus Settles Lawsuit Over Payment Card Breach
Agreement With 43 States Requires Retailer to Use Encryption, Tokenization
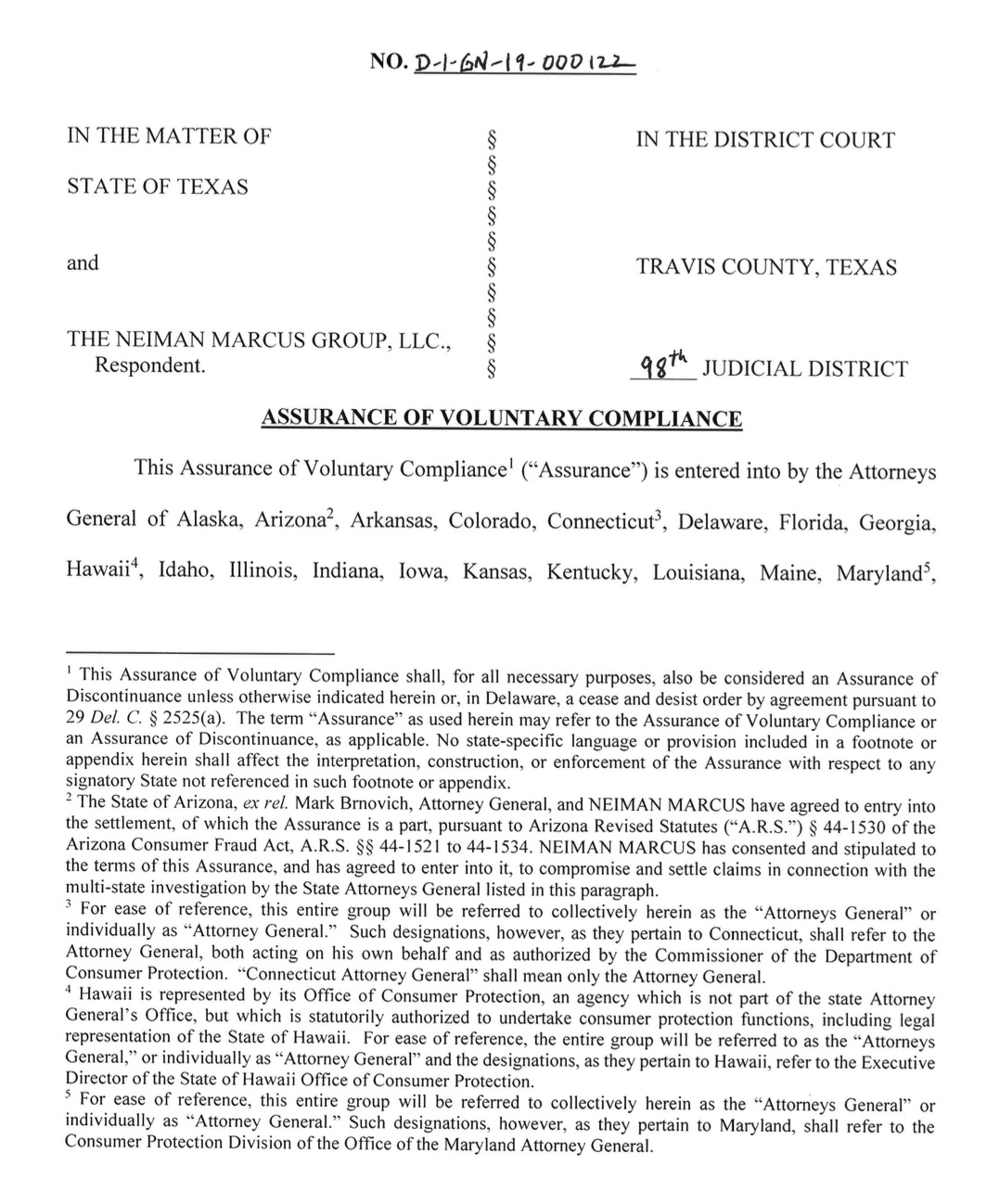
Forty-three states have reached a settlement with Neiman Marcus over its 2013 data breach, one of several breaches from that period blamed on card-scraping malware.
See Also: The State of Organizations' Security Posture as of Q1 2018
Under terms of the deal, the Dallas-based luxury department store chain must pay the states a total of $1.5 million, according to Texas Attorney General Ken Paxton. Neiman Marcus must also put in place security measures to protect plaintext cardholder data.
Attorneys general in Connecticut and Illinois led the legal action against the retailer.
Neiman Marcus revealed the breach in January 2014, just a few weeks after Target said malware scraped about 40 million of its customers' payment card details. The breaches marked a new era in which attackers unleashed determined, large-scale efforts aimed at stealing payment card details.
At Neiman Marcus, the card-scraping malware, active between July and October 2013, grabbed information for 370,000 payment cards. At least 9,200 of those cards were fraudulently used, Paxton says.
Consumers filed six class-action suits against Neiman Marcus as a result of the breach, according to the company's latest annual report. Five were voluntarily dismissed. For the sixth suit, a federal court in Illinois in September 2018 decertified the settlement class, and no settlement remains pending.
Neiman Marcus suffered another, albeit smaller, breach in 2015. In that incident, an attacker accessed 5,200 accounts and used at least 70 of them to make fraudulent purchases. The breach exposed names, stored contact information, purchase histories and the last four digits of payment card numbers (see: Neiman Marcus: 2015 Breach Exposed Full Card Details).
Notification Concerns
Coming just after Target's mega-breach, Neiman's 2014 breach notification contributed to the rising concerns about the security of payment card processing systems.
The breach also triggered questions from lawmakers. Sen. Richard Blumenthal, D-Conn., wrote to Neiman Marcus on Jan. 14, 2014, asking why the company didn't immediately notify affected consumers.
In a letter to Blumenthal, the CIO of Neiman Marcus at the time, Michael R. Kingston, said that the retailer was unaware that it systems had been penetrated until it was contacted by its merchant processor on Dec. 13, 2013. The merchant processor had in turn been alerted by Visa, after it detected the fraudulent use of cards at a small number Neiman Marcus stores.
It wasn't until Jan. 2, 2014, that one of two digital forensic firms retained by the department store chain confirmed that malware had covertly collected payment card details, Kingston wrote. The malware was complex, and encrypted the stolen payment card data before exfiltration, which investigators then needed to decrypt, he explained.
"It was only after this decryption process was concluded that we were able to determine that payment card information had been captured," Kingston wrote.
Attackers snuck malware onto systems inside 77 Neiman Marcus stores. The retailer doesn't appear to have ever confirmed the strain of malware that attackers used, although at the time, many security experts believed that it was similar to the card-scraping malware used against Target.
That type of malware, known as RAM scraper, captures data when a card gets swiped and when the data is still in the memory of a point-of-sale system. Many security experts suspect that Target was hit with a variant of RAM-scraping malware called Kaptoxa - potato in Russian - which is sometimes referred to as BlackPOS.
The malware that infected POS systems at Neiman Marcus wasn't completely disabled until Jan. 10, 2014, Kingston wrote. That same day, Neiman Marcus began sending emails to 2,400 account holders for which it had contact information, and it also began preparing letters for any affected customers for which it had an address on file. Also, then-CEO Karen Katz published a public data breach notification letter on the retailer's website on Jan. 16, 2014.
At the time the breach occurred, Neiman Marcus' systems exceeded the Payment Card Industry's Data Security Standard, or PCI-DSS, requirements, Kingston claimed in his letter to Blumenthal.
Although PCI-DSS compliance is far from a foolproof breach preventer, the advent of memory-scraping malware meant defenders could not necessarily rest easy that their systems were secure, even if they had recently had a clean audit.
Settlement Agreement
As part of the newly announced settlement with states, Neiman Marcus is required to continue to ensure it complies with PCI-DSS. It also must have two digital forensic firms on retainer to investigate incidents, and one of those companies must not have been involved in helping the company comply with PCI-DSS.
On the technology front, Neiman Marcus is required to implement EMV-capable systems, something that Kingston expressed doubt about in early 2014 before a Senate panel due to its immaturity in the U.S. at the time (see: Target, Neiman Marcus Differ on EMV).
The agreement also requires Neiman Marcus to ensure that if attackers manage to steal payment card data, it will be unusable.
"Neiman Marcus shall devalue payment card information, including, but not limited to encryption and/or tokenization, to obfuscate payment card information throughout the course of retail transactions at Neiman Marcus retail locations," the agreement says.