Cybercrime , Cyberwarfare / Nation-State Attacks , Forensics
Microsoft Describes How SolarWinds Hackers Avoided Detection
Attackers Went to Great Lengths to Separate the Backdoor From Loader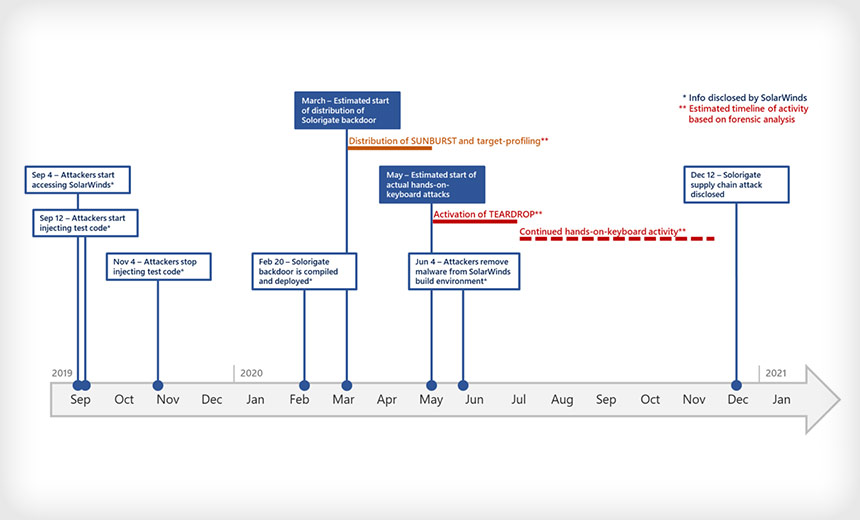
Microsoft researchers are offering fresh details on the SolarWinds hackers’ extensive efforts to remain hidden, which gave them more time to fully penetrate systems, move laterally through networks and exfiltrate data in follow-on attacks.
See Also: The State of Organizations' Security Posture as of Q1 2018
For example, when activating the second stage of an attack, the hackers “went out of their way” to ensure that the backdoor they initially installed in the SolarWinds Orion network monitoring platform was separated “as much as possible” from Cobalt Strike loader implants they used to escalate the attack, paving the way for exfiltrating data.
Microsoft says the attackers apparently believed that this approach meant that if Cobalt Strike - a legitimate penetration testing tool - was detected in an infected system, the victim would not notice the connection to the SolarWinds Orion backdoor.
"The attackers not only carried out an advanced attack but also were very meticulous about covering their tracks," says Hanan Hibshi, teaching scientist at the Information Networking Institute in Carnegie Mellon University’s CyLab Security and Privacy Institute.
The Microsoft report also discusses several previously unknown tactics, techniques and procedures the attackers used, including varying names and folders as well as creating unique Cobalt Strike Dynamic Link Library loaders for each attack.
Scott Shackelford, executive director of the Ostrom Workshop and chair of Indiana University's cybersecurity program, says this report shows how difficult it would have been for security teams to pick up on the attacks.
"The Microsoft report reveals how sophisticated the (SolarWinds) attack really was, given its combination of a supply chain attack and a long-term operation to dig in and move laterally across the compromised networks," he says.
Orion Targeted
The SolarWinds supply chain attack that started in March 2020 involved placing the “Sunburst” backdoor in the company's Orion network monitoring platform so it was downloaded when users updated the software.
While about 18,000 of the company's customers downloaded the infected software, only a few hundred, including government agencies and tech firms, apparently were targeted for the follow-on attacks (see: Severe SolarWinds Hacking: 250 Organizations Affected?).
U.S. intelligence agencies say the attacks appear to be part of a Russian-backed espionage operation.
Deep-Dive Analysis
To help hide their efforts to launch follow-on attacks, the attackers separated Sunburst from Cobalt Strike by using a technique described by MITRE ATT&CK as Event-Triggered Execution: Image File Execution Options Injection, the Microsoft report states. This activated Cobalt Strike when a process called dllhost.exe ran.
"Once the registry value [was] created, the attackers simply [waited] for the occasional execution of dllhost.exe, which might happen naturally on a system," the report says.
The execution of dllhost.exe triggered a launch of wscript.exe that was configured to run a previously dropped VBScript. This, in turn, started rundll32.exe, activating the Cobalt Strike DLL using a clean parent/child process tree completely disconnected from the SolarWinds process, the report says.
The Image File Execution Options Injection was then removed to eliminate any traces of the executed operations, Microsoft says.
Advanced Tactics
The Microsoft researchers say the hackers used professional operational security methods and anti-forensic tactics to remain undiscovered.
For example, each Cobalt Strike DLL implant was unique to the machine it was attacking. Plus, the hackers avoided reusing folder, file or export function names and command-and-control domains.
"Applying this level of permutations for each individual compromised machine is an incredible effort normally not seen with other adversaries and done to prevent full identification of all compromised assets inside a network or effective sharing of threat intel between victims," the report states.
The report describes other hacker behaviors. For example:
- The attackers renamed all the tools and binaries that were used and placed them in folders that mimicked existing programs and files already present on a compromised device.
- Before running noisy network enumeration activities - such as repeated NSLOOKUP or LDAP queries - the attackers carefully prepared special firewall rules to minimize outgoing packets for certain protocols. These were then removed.
- The hackers numerated remote processes and services running on the target host and decided to move laterally only after disabling certain security services.
- The attackers changed time stamps of artifacts and leveraged professional wiping procedures and tools to make it more difficult to find and recover the DLL implants.
The report was prepared by Microsoft's 365 Defender Research Team, Threat Intelligence Center and Cyber Defense Operations Center.