Application Security , Finance & Banking , Fraud Management & Cybercrime
Many Mobile Banking Apps Have Exploitable 'Coding Errors'
Popular Apps Too Susceptible to Hacking, Positive Technologies Warns
Vulnerabilities in a number of mobile banking applications make them susceptible to hacking and customer account data theft, according to the security firm Positive Technologies.
See Also: Bank on Seeing More Targeted Attacks on Financial Services
Researchers at Positive Technologies investigated 14 mobile banking apps that run on Android or iOS and found that 13 failed to prevent unauthorized access to user data. Each of the apps examined in the study had had been downloaded from app stores more than 500,000 times, according to the research report, which does not identify the apps.
The analysis shows that none of the 14 apps studied had an acceptable level of security and that several of the applications contained security flaws and could be exploited without physical access to the smartphone or other mobile device used, according to the report. These types of vulnerabilities can lead to brute-force attacks, man-in-the-middle schemes and the distribution of malware, such as banking Trojans, the researchers say.
Such attacks could provide access to sensitive information, such as the personal banking data and payment card details. Attackers could also gain unauthorized access to the application and commit fraud and steal funds, the report asserts.
"Our research shows that Android apps are more vulnerable than iOS ones," Nikolay Anisenya, the head of mobile application security for Positive Technologies, tells Information Security Media Group. "The vulnerabilities that hackers exploit for fraud and theft are usually the result of coding errors."
Banking Apps Targeted
Threats to online banking have increased recently due to the onset of the COVID-19 pandemic, which has accelerated the switch to mobile banking.
Earlier this month, the FBI issued a warning about cybercriminals and fraudsters increasingly targeting mobile banking apps with malware to steal credentials and conduct account takeover attacks (see: FBI Warns Of Increasing Use of Trojans in Banking Apps)
Another report by security firm Lookout revealed that mobile phishing attacks against banking apps have surged since COVID-19 was declared a pandemic (see: COVID-19 Drives Spike in Mobile Phishing Attacks: Report)
Client-Side Vulnerabilities
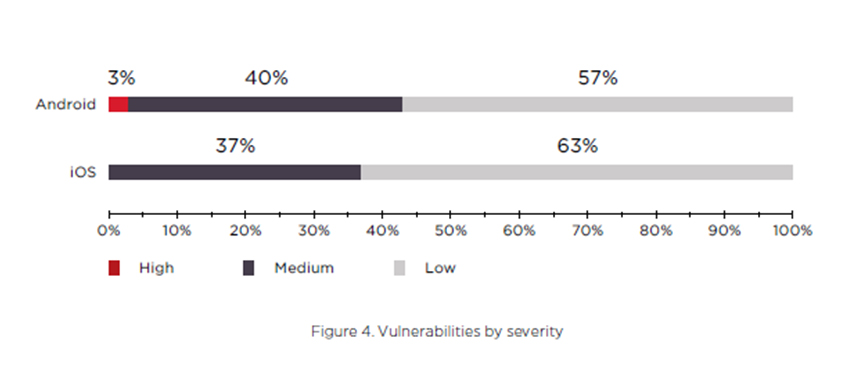
The researchers found that 3% of apps running on Android devices contained vulnerabilities that posed "high" client-side attack risk, 40% posed "medium" threats and 57% contained "low" risks, according to the study. For apps running on iOS devices, the study notes that 37% posed medium risks and 63% had low risk of potential client-side attacks. No iOS-based banking apps contained vulnerabilities considered high-risk.
The study found that banking apps on Android devices contained three to eight flaws, while iOS apps contained four to seven vulnerabilities. The majority of these vulnerabilities originated from the app's source code or insecure data transfer and data storage, according to the study.
The researchers, however, point out that for apps running on Android devices, the most dangerous vulnerabilities stemmed from deep linking technology - a feature that enables the users to navigate between applications.
"Deep linking is used differently on iOS and Android: Developers on Android have more freedom of implementation. This explains the larger number of vulnerabilities in Android applications compared to iOS," according to the report.
Server-Side Vulnerabilities
The study points out that more than half of the banking apps contained high-risk, server-side vulnerabilities related to insufficient authentication, unauthorized access to applications and business logic errors. In most of these apps, the prevalent issue was brute-force vulnerabilities caused the one-time password mechanism, the study says.
"More than half of mobile banks contain high-risk server-side vulnerabilities - for example, insufficient authentication/authorization, password brute-force, business logic errors," Anisenya says. "Unauthorized access to applications usually results from authentication and authorization flaws."
Preventive Measures
Because client-side file systems in most of the banking apps contained unencrypted data, the Positive Technology researchers note the attackers can perform rooting or jail breaking to access the user data. The only way to avoid any potential attack using this method is by storing little data on the user device, requesting data only when needed and deleting data when finished, according to the report.
As for vulnerabilities arising from insecure banking app source code, the Positive Technologies researchers suggest developers should apply a secure software development lifecycle, which helps ensure software is safely created in each stage of its development and security features are integrated into the app.