Cybercrime , Fraud Management & Cybercrime , Next-Generation Technologies & Secure Development
Lebanese Hacking Group Targeting Telcos and ISPs
Researchers: Lebanese Cedar's Campaigns Expand Beyond Middle East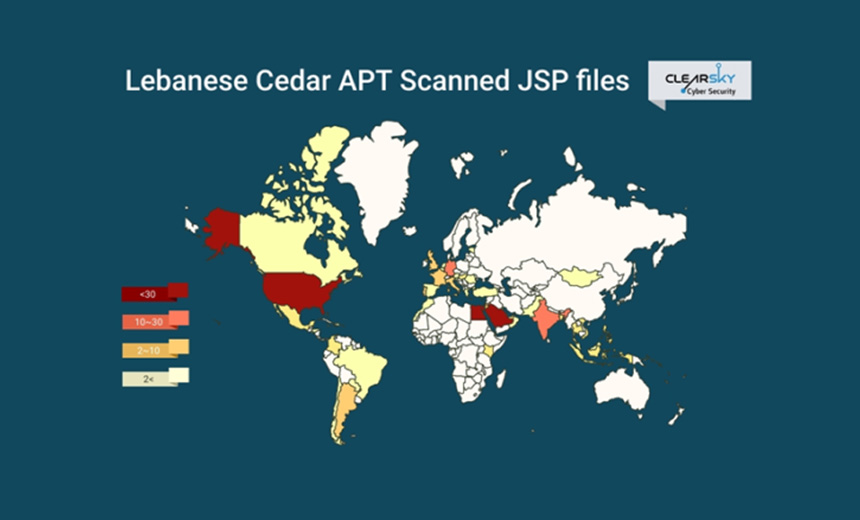
An advanced persistent threat group known as Lebanese Cedar has launched a cyberespionage campaign targeting telecommunication companies and ISPs, according to the Israeli security firm ClearSky.
See Also: Panel Discussion | MITRE ATT&CK Framework: Seeing Through the Eyes of Your Attacker
The report notes that the Lebanese operation, which started in 2020, has spread beyond organizations in the Middle East to include targets in the U.S. and Europe.
Targets of the cyberespionage campaign include several telecommunications firms, including Vodafone Egypt; ISPs, including Middle East Internet Company Ltd. of Saudi Arabia; as well as the Oklahoma Office of Management and Enterprise Services, which serves state agencies, ClearSky says.
The APT group apparently infected about 250 vulnerable web servers with malware, including a remote access Trojan, to steal data, the report notes.
"We assess that there are many more companies that have been hacked and that valuable information was stolen from these companies over periods of months and years," the ClearSky researchers note.
Lebanese Cedar, which is also known as Volatile Cedar and Dancing Salome, has been active since 2012. Security firms, including Check Point and Kaspersky, have tracked its activities. Some analysts believe that the hacking group has ties to the Middle Eastern political and military group Hezbollah, according to ClearSky.
Attack Tactics
Unlike previous campaigns, ClearSky notes, the hackers have now shifted their focus to take advantage of vulnerable public-facing web servers, including those made by Atlassian and Oracle, as part of the initial attack.
The vulnerabilities for which the hackers scan include CVE-2019-3396 in Atlassian Confluence server, CVE-2019-11581 in Atlassian Jira server and CVE-2012-3152 in Oracle's Fusion server, the report notes.
Once the hackers compromise a vulnerable web server, they deploy malicious tools throughout the network, including several types of web shells, such as Caterpillar V2, which enables the attackers to move laterally and deploy additional tools for exfiltrating data.
A hacking tool called JSP file browser gives the hackers the ability to deploy remote web-based file access and helps plant the custom designed “Explosive” RAT malware within infected networks, according to the report.
The hacking group has used that keylogger since 2015. It has self-destruct capabilities as well as machine fingerprinting and memory monitoring functions. The RAT also communicates with command-and-control severs, the report notes.
"We identified the specific open-source JSP file browser that was modified for the hackers’ purposes," the report notes. "We found that Lebanese Cedar deployed the payload of Explosive RAT into the victims' network. Lebanese Cedar is the only known threat actor that uses this code."
Over the past several years, Lebanese Cedar has been tied to several other campaigns, including attacks on defense contractors, telecommunications firms, media companies and educational institutions, according to ClearSky.