Breach Notification , Security Operations , Standards, Regulations & Compliance
House Debates Breach Notification Measure
Bill Would Require Reporting of Critical Infrastructure Attacks Within 72 Hours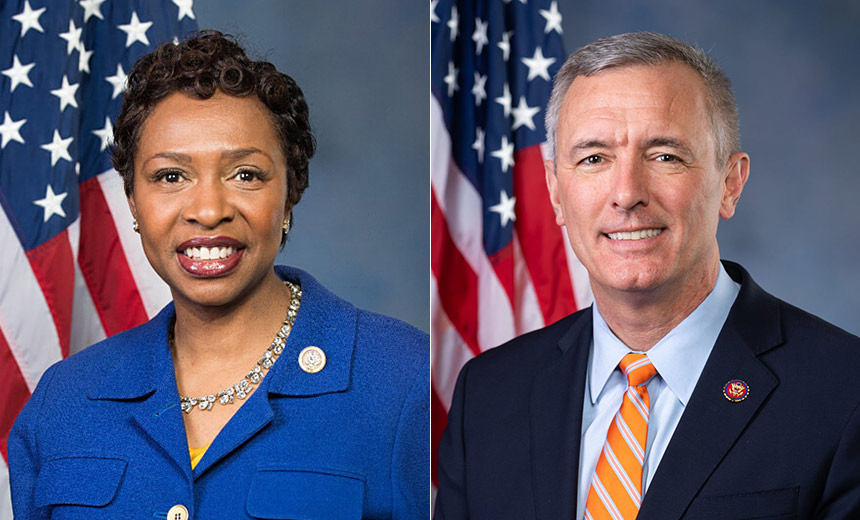
The House began debate Wednesday on legislation that would require companies that own or operate parts of the nation's critical infrastructure to report a cyberattack or breach within 72 hours of confirmation.
See Also: Meeting the Mandate: A Proactive Approach to Cybersecurity Compliance and Incident Reporting
The House Subcommittee on Cybersecurity, Infrastructure Protection & Innovation began debating the bill, the Cyber Incident Reporting for Critical Infrastructure Act of 2021, at a hearing that also included testimony from several cybersecurity experts about the effect the legislation would have on critical infrastructure security and operators.
Unlike a similar breach notification bill in the Senate, the House measure does not describe specific penalties for violations. The Senate bill, which is being debated in the Intelligence Committee, would require incidents to be reported within 24 hours of discovery, rather than 72 hours (see: Senators Introduce Federal Breach Notification Bill) .
Several cybersecurity-related bills have been introduced in the House and Senate in response to recent cyber incidents, including the SolarWinds supply chain attack and the ransomware attack on Colonial Pipeline Co.
Many other national breach notification bills, which would have applied to a broader range of organizations, have failed to advance in Congress over the last several years. The HIPAA Breach Notification Rule, however, requires healthcare organizations to report breaches affecting 500 or more individuals within 60 days of discovery - with smaller breaches reported annually.
Cyber Provisions
The House breach reporting bill would require the U.S. Cybersecurity and Infrastructure Security Agency to create an interim final rule within nine months to determine what critical infrastructure owners and operators would be subject to the 72-hour mandatory reporting rule. This would also include guidelines and rules to determine what type of cyber incidents should be reported to the agency.
The bill also would create a Cyber Incident Review Office that would be housed within CISA. This office would collect and analyze information from these cyber incidents and publish quarterly reports based on that data as well as offer threat intelligence and guidance for first responders.
In addition, the bill would retain CISA's voluntary disclosure program separate from the mandatory one that would send data to the Cyber Incident Review Office. The legislation would also allow CISA to use subpoenas to obtain information about a breach once other reporting avenues have been exhausted, according to the draft document, although specific details about how this would happen have not been worked out.
Finally, the bill would shield cyber incident information given by companies to CISA - unless it's acquired through a subpoena - and also require the agency to alert businesses if they might have been affected by an attack through a federal network.
Bipartisan Support
In formally introducing the notification bill on Wednesday, Rep. Yvette Clarke, D-N.Y., the subcommittee chairman, noted that congressional hearings into the attack against SolarWinds, which led to follow-on attacks on 100 companies and nine federal agencies, showed the need for more mandatory reporting of cyber incidents.
"Our oversight revealed a number of gaps in federal authorities, policies and capabilities that Congress must address to secure its own networks and better serve its private sector partners," Clarke said during her opening remarks. "But what stood out to me was how lucky we were that FireEye disclosed that it had been compromised. Where we would be if they had chosen not to?"
Rep. John Katko, R-N.Y., who serves on the subcommittee and is the ranking member of the full House Committee on Homeland Security, calls for greater visibility across both private and public networks to help counter cyberthreats.
"I hope that everyone here today recognizes our nation's cybersecurity cannot be separated into federal efforts and private efforts, but that it must be a joint effort," Katko said while voicing support for the bill. "Without enhanced collaboration and visibility, we will continue to fall victim to the actors who target our nation, our constituents and all of us on a daily basis."
Expert Testimony
As part of the debate over the House bill, the subcommittee heard testimony from five experts about the provisions in the bill.
Ron Bushar, senior vice president and global government CTO of FireEye Mandiant, testified that companies affected by a cyber incident need time to assess what data may have been lost or stolen.
"Victims require support from external firms to fully analyze a breach and will likely be dealing with other business impacts and crisis management activities," Bushar told lawmakers. "Allowing for a reasonable amount of time to properly assess the situation before requiring reporting will limit false positives, redundant or contradictory information and prevent unnecessary data collection."
Bushar also cautioned against setting penalties for failure to report incidents because companies that are attacked are essentially crime victims. He noted, however, that giving CISA subpoena power to gather information could help in understanding various cyber incidents.
"Although mandatory reporting is necessary, the focus should be on supporting organizations to achieve compliance, not punishment for noncompliance," Bushar said. "Fines and other financial or legal punishments do not properly reflect the truth that, barring gross negligence or willful misconduct, organizations that suffer a cyberattack are victims of a crime."
Heather Hogsett, senior vice president of technology and risk strategy for BITS - the technology policy division of the Bank Policy Institute - commended the bill's 72-hour reporting window and provisions to protect sensitive information and data. The government, however, needs to do more to provide companies with up-to-date threat intelligence, she told the subcommittee.
"We urge Congress to ensure government agencies are improving the speed and quality of the information provided back to critical infrastructure," Hogsett testified.
John Miller, the senior vice president and general counsel of the Information Technology Industry Council, said that CISA should try to gather information about cyber incidents from other sources, such as the FBI, before creating another channel that businesses need to use to submit information following an attack.
"This could be accomplished by directing the Office of Management and Budget to issue guidance to federal regulators and law enforcement requiring agencies to share information related to incidents against covered agencies with the Cyber Incident Review Office," Miller testified.