Fraud Management & Cybercrime , Fraud Risk Management , Next-Generation Technologies & Secure Development
Fresh Wave of Phishing Emails Use Election as a Lure
Proofpoint and KnowBe4 Spot Malicious Messages Disguised as Political Announcements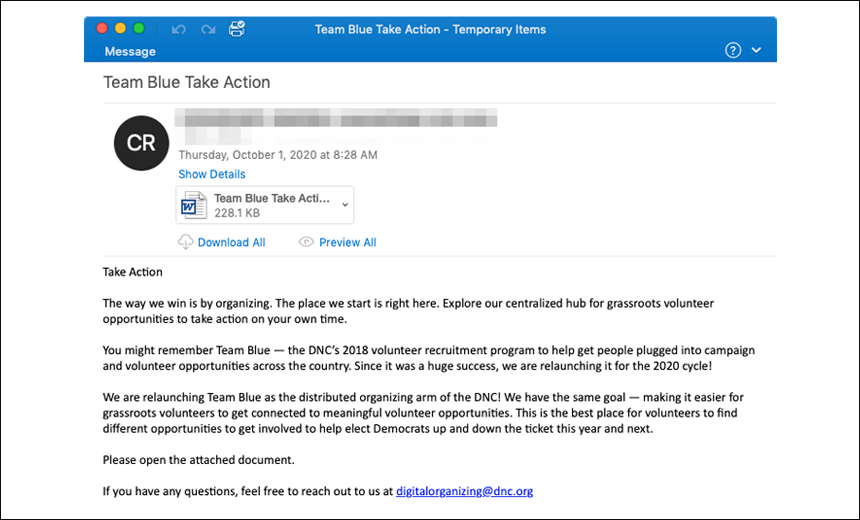
Security researchers are warning of a fresh wave of phishing emails with election-related lures that are designed to get users to click, opening the door to spreading the Emotet botnet or harvesting users' credentials.
See Also: Is Your Email Security Keeping Up with Attackers? Protecting your Microsoft 365 Investment
The security firm Proofpoint has spotted thousands of malicious emails designed to spread Emotet that spoof messages from the Democratic National Committee.
Meanwhile, KnowBe4 has discovered another phishing campaign spoofing the U.S. Election Assistance Commission that’s designed to harvest credentials.
Emotet Campaign
Proofpoint says the latest Emotet campaign, which began on Oct. 1, represents the first time that TA542, the gang behind Emotet, has used a political angle as a phishing lure.
"It's unlikely that this shift is driven by any specific political ideology. Like earlier use of COVID-19 … lure themes, TA542 is attempting to reach as many intended recipients as possible by capitalizing on a popular topic," Proofpoint says.
TA542 is using a combination of techniques designed to convince the recipient the email is coming from a legitimate source. This includes using the subject line "Team Blue Take Action" and lifting messaging directly from a DNC webpage and placing it in the body of the email.
The email's message states that the DNC needs volunteers for the upcoming election and asks the recipient to open an attached Microsoft Word document for additional information. If opened, the attached file downloads Emotet onto the target's computer.
Once Emotet is downloaded, it installs additional modules to steal credentials, harvest emails and spread itself across networks.
Credential Harvesting Scam
KnowBe4 says that the campaign spoofing the Election Assistance Commission “may be part of an attempt by parties unknown to intervene in the election, either by seeding confusion and chaos in the election process or engaging in some form of election fraud - although we judge it more likely that this phish is being used to fuel identity theft and related acts of fraud."
The campaign, spotted on Oct. 1, has not been connected to any group, KnowBe4 says.
The malicious emails carry a message that states: "Your Arizona voter's registration application has been reviewed by your county clerk and some few details could not be confirmed," security researchers say.
A link takes the recipient to a website spoofing ServiceArizona, the legitimate Arizona election information site. The fraudulent site has an online form asking for the person's name, date of birth, mailing address, email address, Social Security number and driver's license information, KnowBe4 says.
"The fact that the email was sent through Sendgrid [a communication platform] - undoubtedly via a compromised account - suggests this phish could have been delivered to a large number of email addresses," KnowBe4 researchers note.
Election Security Warnings
In a recent election-related alert, the FBI and the U.S. Cybersecurity and Infrastructure Security Agency warned that hackers may attempt to conduct distributed denial-of-service attacks on the U.S. election infrastructure (see: FBI, CISA Warn of DDoS Attacks Targeting November Election).
Earlier, the two agencies warned of "foreign actors and cybercriminals" spreading disinformation - claiming to have hacked voter databases - in an attempt to manipulate public opinion, discredit the electoral process and undermine confidence in U.S. democratic institutions (see: FBI, CISA Again Warn of Election Disinformation Campaigns).