Application Security , Cryptocurrency Fraud , Cybercrime
ElectroRAT Malware Targets Cryptocurrency Wallets
Recently Uncovered RAT Can Compromise Windows, Linux and macOS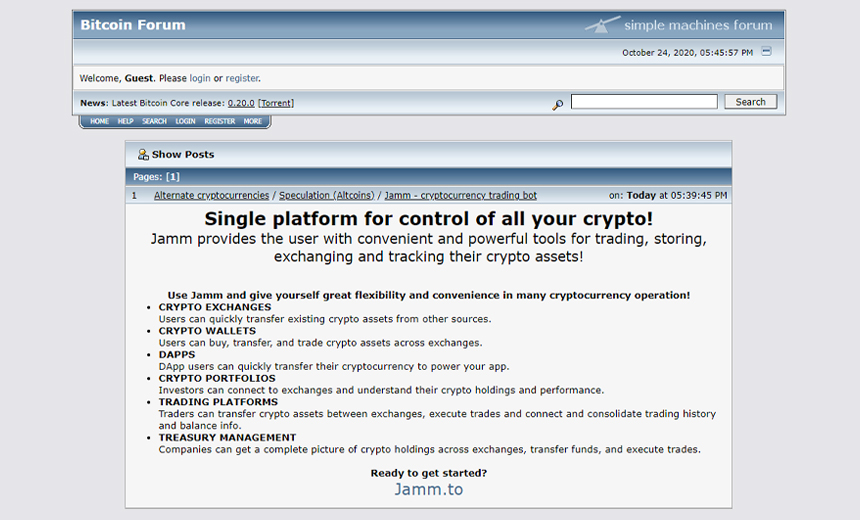
A recently uncovered remote access Trojan, dubbed ElectroRAT, has been stealing cryptocurrency from digital wallets over the past year and has the ability to target multiple operating systems, according to researchers at Intezer Labs.
See Also: OnDemand | API Protection – The Strategy of Protecting Your APIs
The malware, written in the Golang programming language, is designed to target Windows, Linux and macOS platforms and appears to have targeted thousands of victims since early 2020, according to an Intezer Labs report released this week.
The operators behind this campaign have also deployed a series of domain registrations and websites, Trojanized applications and fake social media accounts to target victims and their digital wallets, the report states. The creation of the malware that targets multiple operating systems and appears to have been designed from scratch, however, is the most sophisticated part of this particular campaign.
"It is rather common to see various information stealers trying to collect private keys to access victims’ wallets," Avigayil Mechtinger, a security researcher with Intezer Labs, notes in the report. "However, it is rare to see tools written from scratch and used to target multiple operating systems for these purposes."
Crypto Campaign
In the campaign that Intezer discovered, the operators began by advertising the Trojanized apps on social media platforms, including fake Twitter and Telegram accounts, as well as forums dedicated to discussions and news about cryptocurrency.
The malicious apps were designed to look like legitimate applications for those buying and selling virtual currencies. The operators of this campaign created fake apps called Jamm and eTrade, which appeared to be legitimate cryptocurrency trade management applications, and DaoPoker, which looks like a virtual currency poker app, the report notes.
These weaponized apps disguised the ElectroRAT malware. If the fake apps were downloaded to a device, the victim would see what appeared to be a legitimate user interface. In the background, however, the Trojan would compromise the device, according to the report.

"Once a victim runs the application, an innocent GUI will open, while ElectroRAT runs hidden in the background as 'mdworker,'" the report notes.
The operators behind this campaign created three versions of these Trojanized apps to run on Windows, Linux and macOS. All the apps were created using Electron, an app-building framework.
Kyung Kim, senior managing director and head of cybersecurity for the Asia-Pacific region at FTI Consulting, previously said that more threat actors are using the Golang programming language to help them create malware that can target operating systems other than Windows.
"Golang is popular for attackers because it's multi-variate and allows a single codebase to be accumulated into all major operating systems," Kim said. "Rather than attacking end users, Golang malware focuses its efforts on compromising application servers, frameworks and web applications, which is partially why it can infiltrate systems easily without being detected."
In addition to its ability to drain digital wallets of their cryptocurrency, the ElectroRAT malware works as a keylogger and can take screenshots, upload files from disk, download files to the infected device and execute commands.
The Intezer Labs researchers also found that the ElectroRAT malware will attempt to connect to a Pastebin page to receive the IP address for the command-and-control server controlled by the operators. The report notes that the Pastebin page had been visited about 6,500 times between January and December 2020, which means there are likely thousands of victims who downloaded the malware.