Access Management , Next-Generation Technologies & Secure Development , Threat Detection
China Spies on Russians; Microsoft Details Ukraine Attacks
Chinese Hackers Use Updated PlugX RAT; Microsoft Calls Cyberattacks 'Relentless'
Researchers have observed China-based government-sponsored threat actors collecting intelligence by targeting Russian government officials with an updated variant of a remote access Trojan known as PlugX, a backdoor popular with Chinese-speaking hacker groups.
Cybersecurity firm Secureworks' Counter Threat Unit attributes the current intrusion attempts to the China-based Bronze President threat group because of its use of DLL search order hijacking to execute PlugX malware payloads. Bronze President is also known as Mustang Panda, TA416, HoneyMyte, RedDelta and PKPLUG.
Active since at least July 2018, Bronze President compromises and collects data from nongovernmental organizations and creates multiple contingent access routes for maintaining access to compromised systems for the long term.
The group also uses proprietary and publicly available tools, including Cobalt Strike, China Chopper, PlugX, and RCSession and ORat - the two tools exclusively tied to the group.
"The war in Ukraine has prompted many countries to deploy their cyber capabilities to gain insight about [the] global events, political machinations and motivations. This desire for situational awareness often extends to collecting intelligence from allies and 'friends,' which could explain why [Secureworks] researchers detected what appears to be an attempt by China to deploy advanced malware onto computer systems of Russian officials, the researchers say.
Russia’s own cyber activities have also come under increased scrutiny. On Wednesday, Microsoft released a detailed report about the "relentless and destructive" Russian cyberattacks they observed in the hybrid war" against Ukraine.
"We have seen at least six separate Russia-aligned nation-state actors launch more than 237 operations against Ukraine - including destructive attacks that are ongoing and threaten civilian welfare," says Tom Burt, corporate vice president, customer security and trust, at Microsoft. "The destructive attacks have also been accompanied by broad espionage and intelligence activities."
Burt says that the attacks have degraded the systems of institutions in Ukraine and disrupted citizens' access to reliable information and critical life services on which civilians depend.
Microsoft also says it has observed limited espionage attack activity involving other NATO member states and some disinformation activity.
Decoy Document
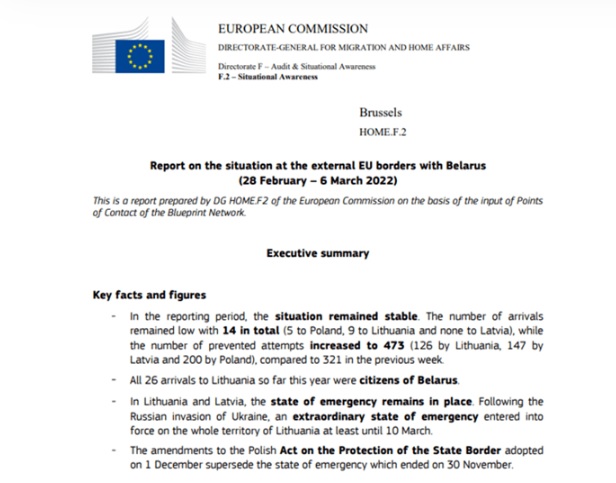
Researchers at CTU in March analyzed a malicious executable file masquerading as a Russian-language document and found that the file's default settings on Windows systems do not display the .exe file extension.
The file was named "Благовещенск - Благовещенский пограничный отряд.exe" or "Blagoveshchensk - Blagoveshchensk Border Detachment.exe".
"The file uses a portable document file icon for credibility. Blagoveshchensk is a Russian city close to the China border and is home to the 56th Blagoveshchenskiy Red Banner Border Guard Detachment. This connection suggests that the filename was chosen to target officials or military personnel familiar with the region," the researchers say.
The heavily obfuscated executable file also downloads files from a staging server.
Researchers say that the executable file displays the decoy document, which is written in English and appears to be legitimate. But researchers at CTU were unable to verify the location of its original source.
The decoy document describes the migratory pressure and asylum applications in countries that border Belarus - Lithuania, Latvia and Poland - and discusses European Union sanctions against Belarus at the beginning of March 2022, the researchers say.
Alan Calder, CEO of U.K.-based IT risk management solutions provider GRC International Group, says this is an example of China shifting its intelligence-gathering activity to focus on information about what is going on in and around the Russian invasion of Ukraine.
"Given that China has borders with Russia and shares a common objective with Russia in terms of overthrowing the current world order - and given the likelihood that the two countries don't share the truth with one another - it's not really surprising that China is actively hunting for intelligence," Calder says.
Technical Analysis
In addition to the file downloaded earlier, the researchers downloaded three more files from the staging server belonging to Bronze President, which it uses for a DLL search order hijacking to execute PlugX malware payloads.
"The inclusion of the ping command with the '-n 70' option adds a significant delay before executing the legitimate signed file. The IP address used for the ping command is Google's public DNS service. The legitimate signed file originates from U.K.-based Global Graphics Software Ltd. Because it is vulnerable to DLL search order hijack, it imports the malicious DocConvDll.dll DLL loader," the researchers say.
This DLL exports eight functions, most of which use random names and contain no useful instructions, the researchers say. The only export called by the parent executable is createSystemFontsUsingEDL.
Researchers say that this createSystemFontsUsingEDL function loads, decrypt and executes FontLog.dat, a corrupt sample that is likely a PlugX payload.
Further analysis of the loader suggests that the malware creates a directory structure under C:ProgramData and copies the three files that DLL sideload and executes the payload to this directory.
"Once PlugX is installed, the malware provides access to the compromised host to extract sensitive system information, upload and download files, and execute a remote command shell," the researchers say.
This particular staging server also hosts the zyber-i .com domain, which has been implicated in a broad PlugX campaign targeting European diplomatic entities. Researchers found that the domain was hosted on 103.107.104.19 from March 2-13, when it served a similarly named group of files for DLL search order hijack.
"Bronze President appears to be changing its targeting in response to the political situation in Europe and the war in Ukraine. The threat group has primarily focused on Southeast Asia, gathering political and economic intelligence valuable to the People's Republic of China (PRC)," the researchers say. "Targeting Russian-speaking users and European entities suggests that the threat actors have received updated tasking that reflects the changing intelligence collection requirements of the PRC."
Microsoft's Warning
When it comes to Russia’s cyber efforts against Ukraine, Microsoft says that known and suspected Russian nation-state actors are working to compromise organizations in regions across the country and are using various techniques - including phishing campaigns, exploiting unpatched vulnerabilities in on-premises Exchange servers and compromising IT service providers - to gain initial access to their targets.
This initial access allows them to destroy, exfiltrate or maintain persistence for a longer period for espionage and surveillance. Threat groups with ties to the GRU, Russia's military intelligence service, have continually developed and used destructive wiper malware or similarly destructive tools on targeted Ukrainian networks since the eve of the invasion.
"From February 23 to April 8, we saw evidence of nearly 40 discrete destructive attacks that permanently destroyed files in hundreds of systems across dozens of organizations in Ukraine," Microsoft's report says.
Microsoft assesses that Russia-aligned threat groups were prepositioning themselves for conflict as early as March 2021, after witnessing threat actors conducting more actions against organizations inside or allied with Ukraine.
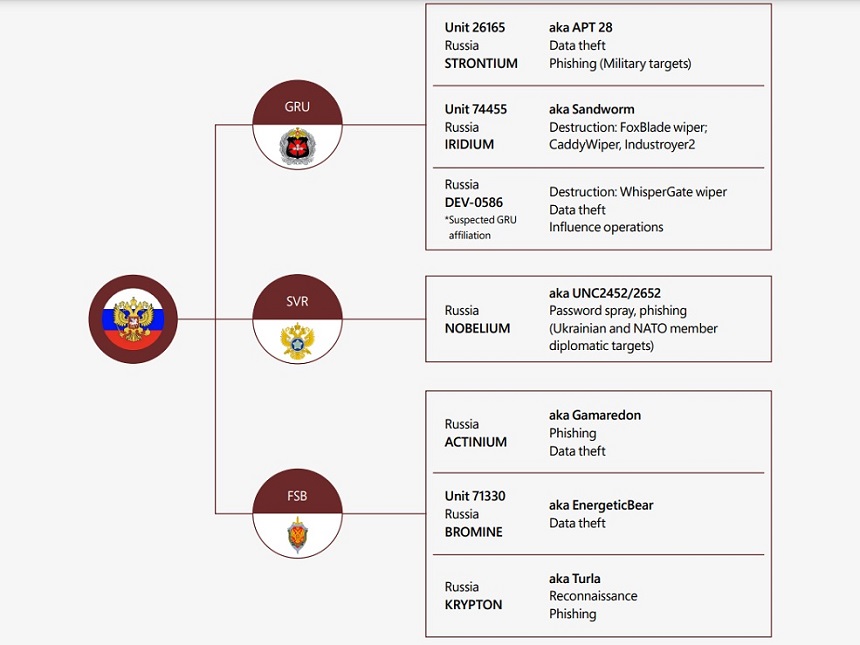
"While we cannot speak to the level of coordination between disparate threat groups, combined, their activities appeared aimed at securing persistent access for strategic and battlefield intelligence collection or to facilitate future destructive attacks in Ukraine during military conflict," Microsoft says.
Microsoft researchers also observed Russian nation-state cyber actors conducting intrusions in concert with kinetic military action.
"Based on our direct engagement with impacted entities in Ukraine, we observed that cyber and kinetic military operations appeared to be directed toward similar military objectives. Threat activity groups often targeted the same sectors or geographic locations around the same time as kinetic military events," Microsoft researchers say.
Further analysis of Microsoft signals with open-source kinetic attack data found that the high concentrations of malicious network activity frequently overlapped with high-intensity fighting during the initial weeks of the invasion.