Access Management , Breach Notification , Cloud Security
Baby's First Data Breach: App Exposes Baby Photos, Videos
Peekaboo Moments Hasn't Responded to Warning That It's Exposing Personal Content
Editors note: About seven hours after this story was published, Peekaboo Moments said it secured the Elasticsearch server and would check its systems for other security problems.
See Also: Securing Email in the Digital Transformation Era
Picture this: A short video features a bundled baby, snoring gently, who flashes a couple of involuntary, sleepy smiles as someone sings a lullaby.
Unfortunately, that video is one of what appear to be thousands of baby videos and images that are being left unsecured and exposed to the internet by Peekaboo Moments, a mobile app. That's because the app's developer, Bithouse Inc., has left an Elasticsearch database open on the internet, warns Dan Ehrlich, who runs Austin, Texas-based computer security consulting firm Twelve Security.
“I've never seen a server so blatantly open,” Ehrlich tells Information Security Media Group. “Everything about the server, the company's website and the iOS/Android app was both bizarrely done and grossly insecure.”
Data, Image and Video Exposure

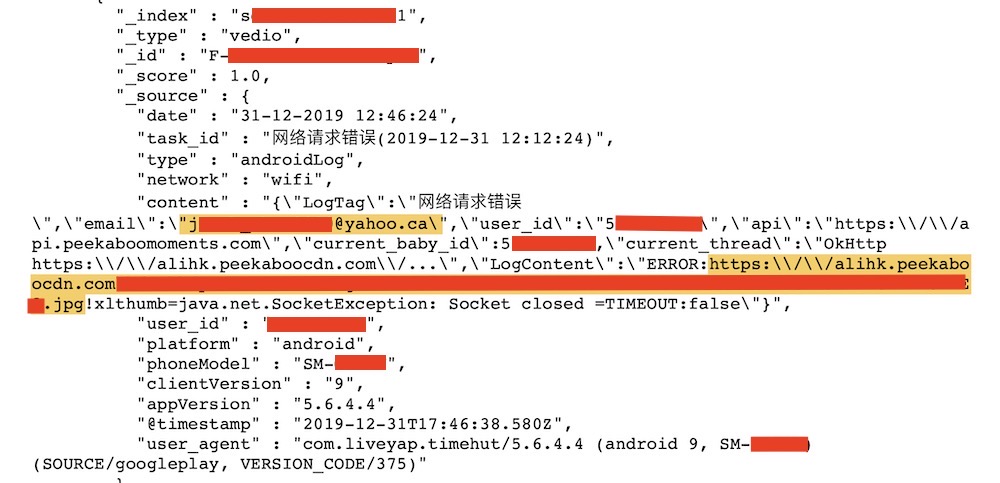
The Peekaboo Moments database contains more than 70 million log files comprising more than 100 GB, with information appearing to date from March 2019, Ehrlich says. The logs record when someone uses the Peekaboo app and the specific action they took at a certain point in time, such as uploading data or content.
Exposed data includes email addresses, detailed device data and often, links to photos and videos, all of which get stored on servers hosted by Singapore-based Alibaba Cloud. Ehrlich estimates that at least 800,000 email addresses are in the exposed data.
The app also transmits sensitive data for babies. It has a growth tracker that allows people to record their baby’s length and weight. It also has a field for a baby’s birthdate. For some of the babies whose data is exposed, this is quite possibly their first data breach exposure.
Another field shows that the app records location data in latitude and longitude to four decimal points, which is accurate to within about 30 feet of an individual's location.
Peekaboo Moments Promises 'Secured Space'
The data exposure alert comes despite Peekaboo Moments describing itself as a “secured space” and promising to safeguard the data and information it stores.
“We completely understand how these moments [are] important to you,” the company writes on its Google Play app profile page. “Data privacy and security come as our priority. Every baby’s photos, audios & videos or diaries will be stored in secured space. Only families and friends can have access to baby’s moments at your control.”
It's not clear for how long Peakaboo's Elasticsearch server has been left unsecured, or who all may have accessed the data.
Repeated efforts by ISMG to contact Peekaboo Moments CEO Jason Liu - based in San Francisco, according to his LinkedIn profile - have been unsuccessful. The company, which appears to be based in China, didn’t respond to emails, and efforts to reach other Peekaboo employees who also appear to be based in China have so far also failed.
ISMG has viewed a small portion of the log data and made an effort to contact a small number of affected users.
Michelle Smith, who lives in Durham, U.K., said she was completely unaware of the data exposure. She’s used the app for seven years for three of her children.
“This is very concerning as I believed it to be a secure app and don't feel comfortable at the thought of strangers being able to access personal pictures,” Smith tells ISMG.
Troy Hunt, a data breach expert who founded the Have I Been Pwned data breach notification service, says that for the most part, Peekaboo’s exposure is a “garden variety” one of the likes that are seen every day. But the exposure of data on children sets it apart, as well as the unresponsiveness to a breach warning.
“Here we have an organisation trusted by a huge number of people to protect their precious memories and they won’t even respond to reports of a very serious data security incident,” Hunt says. “That’s very alarming.”
API Keys Exposed
Ehrlich also noticed other sensitive information, exposed via the database, that puts additional user data at risk.
For example, Peekaboo Moments allows people to take content they’ve uploaded to Facebook and post it within their app. Ehrlich says that the Peekaboo Moments’ API keys for Facebook are also exposed. Those keys could allow an attacker to get access to content on a Peekaboo Moments user’s Facebook page, he says (see: Experts' View: Avoid Social Networks' Single Sign-On).
Ehrlich reported the leak to Facebook on Wednesday.
Facebook did not immediately respond to a query from ISMG regarding the exposure or whether it might revoke the developer's API keys.
Ehrlich also says that Peekaboo Moments has exposed its own API endpoint. That could allow an attacker to upload their own code or exfiltrate all of the data that the API can touch. “It’s pretty standard ‘hacking’ thing to do, and you usually don’t get that lucky,” Ehrlich says (see: Imperva's Breach Post-Mortem: API Key Left Exposed).
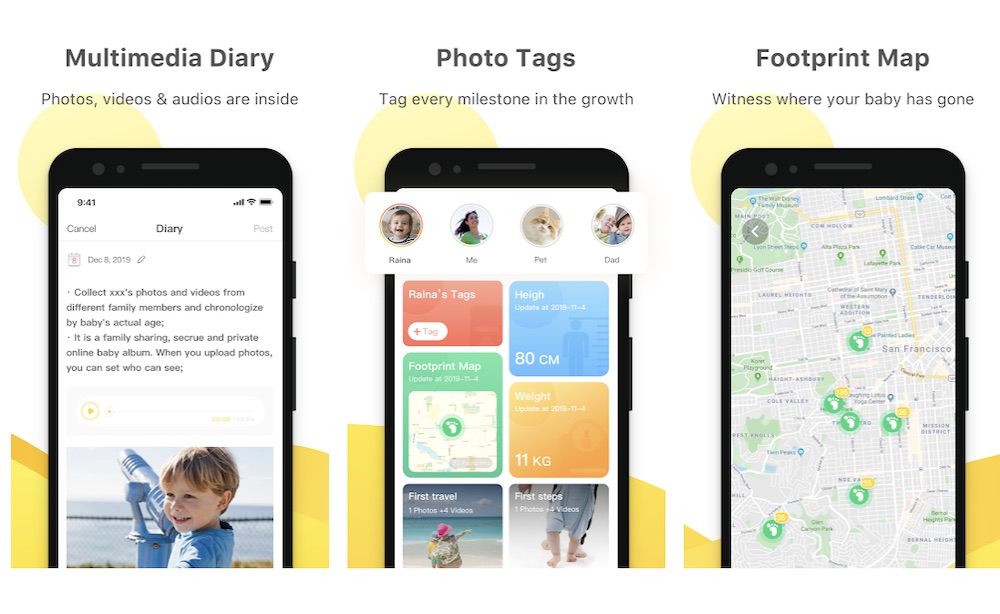
The Peekaboo Moments app is free. The company makes money by offering subscriptions for additional storage, with plans starting at $8.99 per quarter. According to Google Play, the app has been downloaded 1 million times since launching in 2012.
Many recent reviews of the app rate it positively.