Anti-Money Laundering (AML) , Fraud Management & Cybercrime , Fraud Risk Management
20 Arrested in Money-Laundering Crackdown
Group Allegedly Laundered Cash, Cryptocurrency for Other Cybercriminals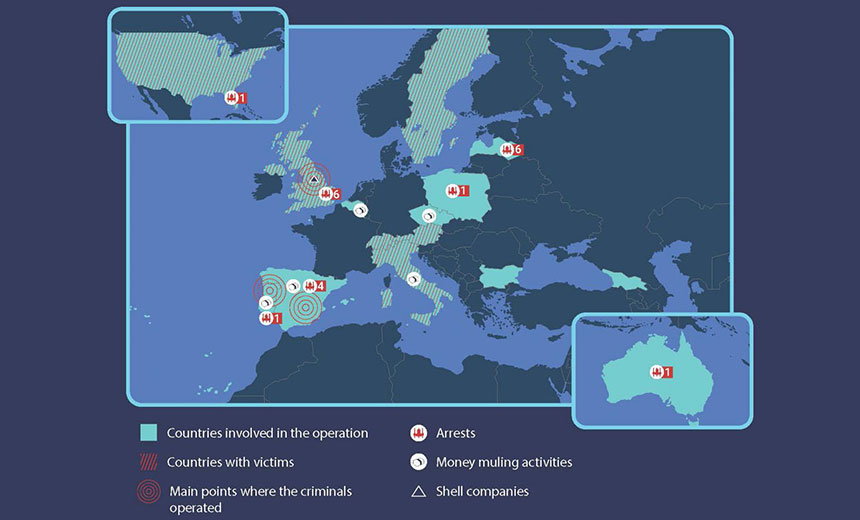
An international law enforcement operation involving 16 countries has resulted in the arrest of 20 individuals suspected of belonging to the QQAAZZ criminal network, which helped launder cash and cryptocurrency for other cybercriminals, according to the U.S. Justice Department and Europol.
A U.S. federal grand jury indictment unsealed Thursday charges 14 individuals from Georgia, Romania, Latvia, Bulgaria and Belgium with providing money-laundering services to high-level cybercriminals. Six others were previously arrested and charged with money laundering, according to the Justice Department.
The money laundering charges carry a possible 20-year federal prison sentence, according to the Justice Department.
The latest arrests came after more than 40 house searches spread across Latvia, Bulgaria, the U.K., Spain and Italy. The largest number of house raids were conducted in Latvia. Bitcoin mining equipment was seized in Bulgaria, according to Europol.
"QQAAZZ advertised its services as a 'global, complicit bank drops service' on Russian-speaking online cybercriminal forums where cybercriminals gather to offer or seek specialized skills or services needed to engage in a variety of cybercriminal activities," according to the Justice Department.
Criminal organizations that allegedly used QQAAZZ's money-laundering skills include those gangs operating well-known malware, such as Dridex, Trickbot and GozNym, the Justice Department reports (see: Two Russians Indicted Over $100M Dridex Malware Thefts).
Allegations Against QQAAZZ
U.S. authorities allege the QQAAZZ network laundered, or attempted to launder, tens of millions of dollars stolen from cybercrime victims since 2016.
The QQAAZZ cybercrime group comprises individuals from more than a dozen countries, according to Europol.
The group registered dozens of shell companies it used to open hundreds of corporate bank accounts at financial institutions in several countries, including the U.K., Portugal, Spain, Germany, Belgium, Turkey and the Netherlands, according to the court documents. These accounts were used to receive and launder stolen money, the Justice Department alleges.
"The funds were then transferred to other QQAAZZ-controlled bank accounts and sometimes converted to cryptocurrency using 'tumbling' services designed to hide the source of the funds. After taking a fee of up to 40% to 50%, QQAAZZ returned the balance of the stolen funds to their cybercriminal clientele," according to the Justice Department.
U.S. victims that had money stolen include several Pittsburgh banks, a Jewish orthodox synagogue in Brooklyn and a medical device manufacturer in York, Pennsylvania, prosecutors say.
Earlier Arrests
In January, the U.S. Department of Justice indicted five Latvian nationals on charges of providing money-laundering services for cybercriminals as part of QQAAZZ. One of the men indicted, Aleksejs Trofimovics, was alleged to have run a virtual currency exchange website that was seized by law enforcement in 2017.
In April, the FBI arrested a Russian national for allegedly helping QQAAZZ launder money by turning cash into bitcoin and other cryptocurrencies (see: FBI Alleges Russian Man Laundered Cybercriminals' Money). Maksim Boiko was arrested by FBI agents on March 28 in Miami and is in federal custody.
Arkady Bukh, a Brooklyn-based attorney representing Boiko, tells Information Security Media Group that his client has pleaded not guilty and likely will face trial next year.